rex
Description
Use this command to either extract fields using regular expression named groups, or replace or substitute characters in a field using sed expressions.
The rex command matches the value of the specified field against the unanchored regular expression and extracts the named groups into fields of the corresponding names.
When mode=sed, the given sed expression used to replace or substitute characters is applied to the value of the chosen field. This sed-syntax is also used to mask, or anonymize, sensitive data at index-time. Read about using sed to anonymize data in the Getting Data In Manual.
If a field is not specified, the regular expression or sed expression is applied to the _raw field. Running the rex command against the _raw field might have a performance impact.
Use the rex command for search-time field extraction or string replacement and character substitution.
Syntax
The required syntax is in bold.
- rex [field=<field>]
- ( <regex-expression> [max_match=<int>] [offset_field=<string>] ) | (mode=sed <sed-expression>)
Required arguments
You must specify either <regex-expression> or mode=sed <sed-expression>.
- regex-expression
- Syntax: "<string>"
- Description: The PCRE regular expression that defines the information to match and extract from the specified field.
- mode
- Syntax: mode=sed
- Description: Specify to indicate that you are using a sed (UNIX stream editor) expression.
- sed-expression
- Syntax: "<string>"
- Description: When mode=sed, specify whether to replace strings (s) or substitute characters (y) in the matching regular expression. No other sed commands are implemented. Sed mode supports the following flags: global (g) and Nth occurrence (N), where N is a number that is the character location in the string.
Optional arguments
- field
- Syntax: field=<field>
- Description: The field that you want to extract information from.
- Default:
_raw
- max_match
- Syntax: max_match=<int>
- Description: Controls the number of times the regex is matched. If greater than 1, the resulting fields are multivalued fields. Use 0 to specify unlimited matches. Multiple matches apply to the repeated application of the whole pattern. If your regex contains a capture group that can match multiple times within your pattern, only the last capture group is used for multiple matches.
- Default: 1
- offset_field
- Syntax: offset_field=<string>
- Description: Creates a field that lists the position of certain values in the
fieldargument, based on the regular expression specified inregex-expression. For example, if therexexpression is"(?<tenchars>.{10})"the first ten characters of thefieldargument are matched. Theoffset_fieldshowstenchars=0-9. The offset calculation always uses zero ( 0 ) for the first position. For another example, see Examples. - Default: No default
Usage
The rex command is a distributable streaming command. See Command types.
rex command or regex command?
Use the rex command to either extract fields using regular expression named groups, or replace or substitute characters in a field using sed expressions.
Use the regex command to remove results that do not match the specified regular expression.
Regular expressions
Splunk SPL supports perl-compatible regular expressions (PCRE).
When you use regular expressions in searches, you need to be aware of how characters such as pipe ( | ) and backslash ( \ ) are handled. See SPL and regular expressions in the Search Manual.
For general information about regular expressions, see About Splunk regular expressions in the Knowledge Manager Manual.
Sed expressions
When using the rex command in sed mode, you have two options: replace (s) or character substitution (y).
The syntax for using sed to replace (s) text in your data is: "s/<regex>/<replacement>/<flags>"
- <regex> is a PCRE regular expression, which can include capturing groups.
- <replacement> is a string to replace the regex match. Use
\nfor back references, where "n" is a single digit. - <flags> can be either
gto replace all matches, or a number to replace a specified match.
The syntax for using sed to substitute characters is: "y/<string1>/<string2>/"
- This substitutes the characters that match <string1> with the characters in <string2>.
When using the rex command in sed mode, the rex command supports the same sed expressions as the SEDCMD setting in the props.conf.in file.
Anonymize multiline text using sed expressions
The Splunk platform doesn't support applying sed expressions in multiline mode. To use a sed expression to anonymize multiline events, use 2 sed expressions in succession by first removing the newlines and then performing additional replacements. For example, the following search uses the rex command to replace all newline characters in a multiline event containing HTML content, and then redacts all of the HTML content.
index=main html
| rex mode=sed field=_raw "s/\\n/NEWLINE_REMOVED/g"
| rex mode=sed field=_raw "s/<html.*html>/REDACTED/g"
Examples
1. Extract email values using regular expressions
Extract email values from events to create from and to fields in your events. For example, you have events such as:
Mon Mar 19 20:16:27 2018 Info: Bounced: DCID 8413617 MID 19338947 From: <MariaDubois@example.com> To: <zecora@buttercupgames.com> RID 0 - 5.4.7 - Delivery expired (message too old) ('000', ['timeout'])
Mon Mar 19 20:16:03 2018 Info: Delayed: DCID 8414309 MID 19410908 From: <WeiZhang@example.com> To: <mcintosh@buttercupgames.com> RID 0 - 4.3.2 - Not accepting messages at this time ('421', ['4.3.2 try again later'])
Mon Mar 19 20:16:02 2018 Info: Bounced: DCID 0 MID 19408690 From: <Exit_Desk@sample.net> To: <lyra@buttercupgames.com> RID 0 - 5.1.2 - Bad destination host ('000', ['DNS Hard Error looking up mahidnrasatyambsg.com (MX): NXDomain'])
Mon Mar 19 20:15:53 2018 Info: Delayed: DCID 8414166 MID 19410657 From: <Manish_Das@example.com> To: <dash@buttercupgames.com> RID 0 - 4.3.2 - Not accepting messages at this time ('421', ['4.3.2 try again later'])
When the events were indexed, the From and To values were not identified as fields. You can use the rex command to extract the field values and create from and to fields in your search results.
The from and to lines in the _raw events follow an identical pattern. Each from line is From: and each to line is To:. The email addresses are enclosed in angle brackets. You can use this pattern to create a regular expression to extract the values and create the fields.
source="cisco_esa.txt" | rex field=_raw "From: <(?<from>.*)> To: <(?<to>.*)>"
You can remove duplicate values and return only the list of address by adding the dedup and table commands to the search.
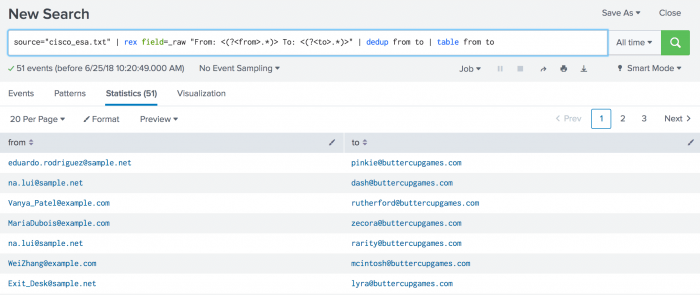
source="cisco_esa.txt" | rex field=_raw "From: <(?<from>.*)> To: <(?<to>.*)>" | dedup from to | table from to
The results look something like this:
2. Extract from multi-valued fields using max_match
You can use the max_match argument to specify that the regular expression runs multiple times to extract multiple values from a field.
For example, use the makeresults command to create a field with multiple values:
| makeresults
| eval test="a$1,b$2"
The results look something like this:
| _time | test |
|---|---|
| 2019-12-05 11:15:28 | a$1,b$2 |
To extract each of the values in the test field separately, you use the max_match argument with the rex command. For example:
...| rex field=test max_match=0 "((?<field>[^$]*)\$(?<value>[^,]*),?)"
The results look something like this:
| _time | field | test | value |
|---|---|---|---|
| 2019-12-05 11:36:57 | a
b |
a$1,b$2 | 1
2 |
3. Extract values from a field in scheduler.log events
Extract "user", "app" and "SavedSearchName" from a field called "savedsearch_id" in scheduler.log events. If savedsearch_id=bob;search;my_saved_search then user=bob , app=search and SavedSearchName=my_saved_search
... | rex field=savedsearch_id "(?<user>\w+);(?<app>\w+);(?<SavedSearchName>\w+)"
4. Use a sed expression
Use sed syntax to match the regex to a series of numbers and replace them with an anonymized string.
... | rex field=ccnumber mode=sed "s/(\d{4}-){3}/XXXX-XXXX-XXXX-/g"
5. Use a sed expression with capture replace for strings
This example shows how to use the rex command sed expression with capture replace using \1, \2 to reuse captured pieces of a string.
This search creates an event with three fields, _time, search, and orig_search. The regular expression removes the quotation marks and any leading or trailing spaces around the quotation marks.
|makeresults
|eval orig_search="src_ip=TERM( \"10.8.2.33\" ) OR src_ip=TERM( \"172.17.154.197\" )", search=orig_search
|rex mode=sed field=search "s/\s\"(\d+\.\d+\.\d+\.\d+)\"\s/\1/g"
The results look like this:
| _time | orig_search | search |
|---|---|---|
| 2021-05-31 23:36:29 | src_ip=TERM( "10.8.2.33" ) OR src_ip=TERM( "172.17.154.197" ) | src_ip=TERM(10.8.2.33) OR src_ip=TERM(172.17.154.197) |
6. Use an offset_field
To identify the position of certain values in a field, use the rex command with the offset_field argument and a regular expression.
The following example starts with the makeresults command to create a field with a value:
| makeresults
| eval list="abcdefghijklmnopqrstuvwxyz"
The results look something like this:
| _time | list |
|---|---|
| 2022-05-21 11:36:57 | abcdefghijklmnopqrstuvwxyz |
Add the rex command with the offset_field argument to the search to create a field called off. You can identify the position of the first five values in the field list using the regular expression "(?<firstfive>abcde)". For example:
| makeresults
| eval list="abcdefghijklmnopqrstuvwxyz"
| rex offset_field=off field=list "(?<firstfive>abcde)"
The results look something like this:
| _time | firstfive | list | off |
|---|---|---|---|
| 2022-05-21 11:36:57 | abcde | abcdefghijklmnopqrstuvwxyz | firstfive=0-4 |
You can identify the position of several of the middle values in the field list using the regular expression "(?<middle>fgh)". For example:
| makeresults
| eval list="abcdefghijklmnopqrstuvwxyz"
| rex offset_field=off field=list "(?<middle>fgh)"
The results look something like this:
| _time | list | middle | off |
|---|---|---|---|
| 2022-05-21 11:36:57 | abcdefghijklmnopqrstuvwxyz | fgh | middle=5-7 |
7. Display IP address and ports of potential attackers
Display IP address and ports of potential attackers.
sourcetype=linux_secure port "failed password" | rex "\s+(?<ports>port \d+)" | top src_ip ports showperc=0
This search uses the rex command to extract the port field and values. The search returns a table that lists the top source IP addresses (src_ip) and ports of the potential attackers.
See also
| reverse | rtorder |
This documentation applies to the following versions of Splunk® Enterprise: 7.1.0, 7.1.1, 7.1.2, 7.1.3, 7.1.4, 7.1.5, 7.1.6, 7.1.7, 7.1.8, 7.1.9, 7.1.10, 7.2.0, 7.2.1, 7.2.2, 7.2.3, 7.2.4, 7.2.5, 7.2.6, 7.2.7, 7.2.8, 7.2.9, 7.2.10, 7.3.0, 7.3.1, 7.3.2, 7.3.3, 7.3.4, 7.3.5, 7.3.6, 7.3.7, 7.3.8, 7.3.9, 8.0.0, 8.0.1, 8.0.2, 8.0.3, 8.0.4, 8.0.5, 8.0.6, 8.0.7, 8.0.8, 8.0.9, 8.0.10, 8.1.0, 8.1.1, 8.1.2, 8.1.3, 8.1.4, 8.1.5, 8.1.6, 8.1.7, 8.1.8, 8.1.9, 8.1.10, 8.1.11, 8.1.12, 8.1.13, 8.1.14, 8.2.0, 8.2.1, 8.2.2, 8.2.3, 8.2.4, 8.2.5, 8.2.6, 8.2.7, 8.2.8, 8.2.9, 8.2.10, 8.2.11, 8.2.12, 9.0.0, 9.0.1, 9.0.2, 9.0.3, 9.0.4, 9.0.5, 9.0.6, 9.0.7, 9.0.8, 9.0.9, 9.0.10, 9.1.0, 9.1.1, 9.1.2, 9.1.3, 9.1.4, 9.1.5, 9.1.6, 9.1.7, 9.1.8, 9.1.9, 9.2.0, 9.2.1, 9.2.2, 9.2.3, 9.2.4, 9.2.5, 9.2.6, 9.3.0, 9.3.1, 9.3.2, 9.3.3, 9.3.4, 9.4.0, 9.4.1, 9.4.2
 Download manual
Download manual
Feedback submitted, thanks!