Search macro examples
Review these search macro use cases and their solutions.
Prerequisites
Simple search macro with argument
The following set of partial searches are nearly identical.
sourcetype="iis" cs_username!="-" /TM/ .pdf
sourcetype="iis" cs_username!="-" /TD/ .pdf
sourcetype="iis" cs_username!="-" /TDB/ .pdf
You want to create a search macro that uses the common parts of this fragment, and that allows you to pass an argument for the variable material between the slashes.
Steps
- Create a search macro named
iis_search(1)with the following definition:sourcetype="iis" cs_username!="-" /$fragment$/ .pdf - In the Arguments field, enter fragment as the argument.
- Click Save.
You can insert `iis_search(fragment=TM)` into your search string to call the search macro for the TM fragment.
Preview your search to see the contents of your macro
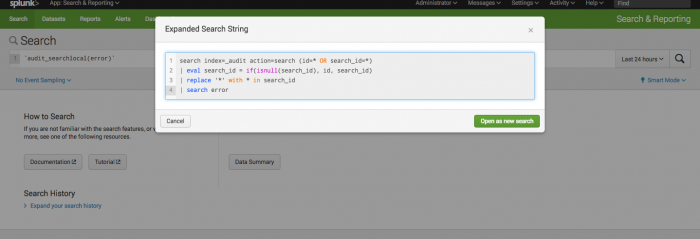
Use the the search preview feature to see the contents of search macros that are embedded within the search, without actually running the search. When you preview a search, the feature expands all of the macros within the search, including macros that are nested within other macros.
Steps
- Navigate to the Splunk Search page.
- In the Search bar, type the default macro
`audit_searchlocal(error)`. - Use the keyboard shortcut Command-Shift-E (Mac OSX) or Control-Shift-E (Linux or Windows) to open the search preview.
The search preview displays syntax highlighting and line numbers, if those features are enabled. - (Optional) Copy a fragment of the search.
- (Optional) Click Open in Search to run the expanded search in a new browser window.
Combine search macros and transactions
You can combine transactions and macro searches to simplify your transaction searches and reports. The following example demonstrates how you can use search macros to build reports based on a defined transaction.
A search macro named makesessions defines a transaction session from events that share the same clientip value, and that occur within 30 minutes of each other. Following is the definition of makesessions:
transaction clientip maxpause=30m
The following search uses the makesessions search macro to take web traffic events and break them into sessions:
sourcetype=access_* | `makesessions`
The following search uses the makesessions search macro to return a report of the number of pageviews per session for each day:
sourcetype=access_* | `makesessions` | timechart span=1d sum(eventcount) as pageviews count as sessions
To build the same report with varying span lengths, save the report as a search macro with an argument for the span length. Name the macro pageviews_per_session(1). The macro references the original makesessions macro. Following is the definition for this macro:
sourcetype=access_* | `makesessions` | timechart $span$ sum(eventcount) as pageviews count as sessions
When you insert the pageviews_per_session(1) macro into a search string, you use the argument to specify a span length.
`pageviews_per_session(span=1h)`
Validate arguments to determine whether they are numeric
The following example demonstrates search macro argument validation.
Steps
- Select Settings > Advanced Search > Search Macros.
- Click New Search Macro to create a new search macro.
- For Name, enter newrate(2). The (2) indicates that the macro contains two arguments.
- For Definiton, enter the following:
This definition includes the argument variableseval new_rate=$val$*$rate$valandrate. - For the Arguments field, enter val and rate.
- Enter a Validation expression that verifies that the value supplied for rate is numeric, as follows:
isnum($rate$) - Enter the following Validation error message: "The rate value that you provided is not numeric. Enter a numeric rate value."
- Click Save.
When another user includes the newrate(2) macro in a search, they might fill out the arguments like this: `newrate(revenue, 0.79)`.
If they leave the 0 out (`newrate(revenue, .79)`) the macro is invalid because the value .79 lacks a leading zero and is interpreted as a string. To ensure that the argument is read as a floating point number, the user should use the tonumber function as follows: `newrate(revenue, tonumber(.79))`
| Define search macros in Settings | Dataset types and usage |
This documentation applies to the following versions of Splunk® Enterprise: 7.0.0, 7.0.1, 7.0.2, 7.0.3, 7.0.4, 7.0.5, 7.0.6, 7.0.7, 7.0.8, 7.0.9, 7.0.10, 7.0.11, 7.0.13, 7.1.0, 7.1.1, 7.1.2, 7.1.3, 7.1.4, 7.1.5, 7.1.6, 7.1.7, 7.1.8, 7.1.9, 7.1.10, 7.2.0, 7.2.1, 7.2.2, 7.2.3, 7.2.4, 7.2.5, 7.2.6, 7.2.7, 7.2.8, 7.2.9, 7.2.10, 7.3.0, 7.3.1, 7.3.2, 7.3.3, 7.3.4, 7.3.5, 7.3.6, 7.3.7, 7.3.8, 7.3.9, 8.0.0, 8.0.1, 8.0.2, 8.0.3, 8.0.4, 8.0.5, 8.0.6, 8.0.7, 8.0.8, 8.0.9, 8.0.10, 8.1.0, 8.1.1, 8.1.2, 8.1.3, 8.1.4, 8.1.5, 8.1.6, 8.1.7, 8.1.8, 8.1.9, 8.1.10, 8.1.11, 8.1.12, 8.1.13, 8.1.14, 8.2.0, 8.2.1, 8.2.2, 8.2.3, 8.2.4, 8.2.5, 8.2.6, 8.2.7, 8.2.8, 8.2.9, 8.2.10, 8.2.11, 8.2.12, 9.0.0, 9.0.1, 9.0.2, 9.0.3, 9.0.4, 9.0.5, 9.0.6, 9.0.7, 9.0.8, 9.0.9, 9.0.10, 9.1.0, 9.1.1, 9.1.2, 9.1.3, 9.1.4, 9.1.5, 9.1.6, 9.1.7, 9.1.8, 9.1.9, 9.2.0, 9.2.1, 9.2.2, 9.2.3, 9.2.4, 9.2.5, 9.2.6, 9.3.0, 9.3.1, 9.3.2, 9.3.3, 9.3.4, 9.4.0, 9.4.1, 9.4.2
 Download manual
Download manual
Feedback submitted, thanks!