Classify and group similar events
An event is not the same thing as an event type. An event is a single instance of data — a single log entry, for example. An event type is a classification used to label and group events.
The names of the matching event types for an event are set on the event, in a multivalue field called eventtype. You can search for these groups of events (for example, SSH logins) the same way you search for any field value.
This topic discusses how to classify events (save a search as an event type) and search for tagged fields. For more information about events, how Splunk software recognizes them, and what it does when it processes them for indexing, see the Overview of event processing topic in the Getting Data In manual.
Important: You cannot save a search pipeline as an event type; that is, when saving a search as an event type, it cannot include a search command.
Save a search as a new event type
When you search your event data, you are essentially filtering out all unwanted events. The results of your search are events that share common characteristics, and you can give them a collective name.
For example, if you often search for failed logins on different host machines, you can save an event type for the events and call it failed_login:
"failed login" OR "FAILED LOGIN" OR "Authentication failure" OR "Failed to authenticate user"
To save this search as an event type:
- Click Save As and select Event Type.
- In Save As Event Type window, give your event type a Name.
In this example the name is failed_login.
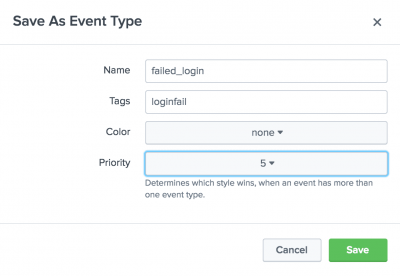
You can add a list of tags that should be applied to the event type in the Tag(s) field. For more about tags see the section Use tags to group and find similar events below. - Click Save to save your event type name.
Now, you can quickly search for all the events that match this event type the same way you can search for any field, by specifying the event type in your search criteria.
For example, you might be interested in finding failed logins on specific host machines. Your search might look something like this:
host=target eventtype=failed_login
Or you might want to investigate suspicious user activity. Your search might look something like this:
user=suspicious eventtype=failed_login
Use findtypes to discover new event types
Pass any of your searches into the findtypes command to display suggestions for event types. The findtypes command compares the events resulting from the search and groups those events that have similar punctuation and terms together.
For more information and examples, see "findtypes" in the search command reference.
Use tags to group and find similar events
In your data, you might have groups of events with related field values. To help you search more efficiently for these groups of fields, you can assign tags to their field values. You can assign one or more tags to any extracted field (including event type, host, source, or source type).
Event types can have one or more tags associated with them. You can add these tags while you save a search as an event type and from the event type manager, located in Manager > Event types. From the list of event types in this window, select the one you want to edit.
After you add tags to your event types, you can search for them in the same way you search for any tag. Let's say you saved a search for firewall events as the event type firewall_allowed, and then saved a search for login events as the event type login_successful. If you tagged both of these event types with allow, all events of either of those event types can be retrieved by using the search:
tag::eventtype="allow"
You can tag field/value pairs. You can also alias field names. See Tag field value pairs in Search and Create field aliases in Splunk Web.
Search for tagged field values
There are two ways to search for tags. If you are searching for a tag associated with a value on any field, you can use the following syntax:
tag=<tagname>
Or, if you are looking for a tag associated with a value on a specific field, you can use the following syntax:
tag::<field>=<tagname>
Use wildcards to search for tags
You can use the asterisk (*) wildcard when searching keywords and field values, including for eventtypes and tags.
For example, if you have multiple event-type tags for various types of IP addresses, such as IP-src and IP-dst, you can search for all of them with:
tag::eventtype=IP-*
If you wanted to find all hosts whose tags contain "local", you can search for the tag:
tag::host=*local*
Also, if you wanted to search for the events with eventtypes that have no tags, you can search for the Boolean expression:
NOT tag::eventtype=*
| Search across one or more distributed search peers | Use the timeline to investigate events |
This documentation applies to the following versions of Splunk® Enterprise: 7.0.0, 7.0.1, 7.0.2, 7.0.3, 7.0.4, 7.0.5, 7.0.6, 7.0.7, 7.0.8, 7.0.9, 7.0.10, 7.0.11, 7.0.13, 7.1.0, 7.1.1, 7.1.2, 7.1.3, 7.1.4, 7.1.5, 7.1.6, 7.1.7, 7.1.8, 7.1.9, 7.1.10, 7.2.0, 7.2.1, 7.2.2, 7.2.3, 7.2.4, 7.2.5, 7.2.6, 7.2.7, 7.2.8, 7.2.9, 7.2.10, 7.3.0, 7.3.1, 7.3.2, 7.3.3, 7.3.4, 7.3.5, 7.3.6, 7.3.7, 7.3.8, 7.3.9, 8.0.0, 8.0.1, 8.0.2, 8.0.3, 8.0.4, 8.0.5, 8.0.6, 8.0.7, 8.0.8, 8.0.9, 8.0.10, 8.1.0, 8.1.1, 8.1.2, 8.1.3, 8.1.4, 8.1.5, 8.1.6, 8.1.7, 8.1.8, 8.1.9, 8.1.10, 8.1.11, 8.1.12, 8.1.13, 8.1.14, 8.2.0, 8.2.1, 8.2.2, 8.2.3, 8.2.4, 8.2.5, 8.2.6, 8.2.7, 8.2.8, 8.2.9, 8.2.10, 8.2.11, 8.2.12, 9.0.0, 9.0.1, 9.0.2, 9.0.3, 9.0.4, 9.0.5, 9.0.6, 9.0.7, 9.0.8, 9.0.9, 9.0.10, 9.1.0, 9.1.1, 9.1.2, 9.1.3, 9.1.4, 9.1.5, 9.1.6, 9.1.7, 9.1.8, 9.1.9, 9.2.0, 9.2.1, 9.2.2, 9.2.3, 9.2.4, 9.2.5, 9.2.6, 9.3.0, 9.3.1, 9.3.2, 9.3.3, 9.3.4, 9.4.0, 9.4.1, 9.4.2
 Download manual
Download manual
Feedback submitted, thanks!