Managing app and add-on configurations and properties
You can manage the configurations and properties for apps installed in your Splunk Enterprise instance from the Apps menu. Click on Apps in the User bar to select one of your installed apps or manage an app. From the Manage Apps page, you can do the following:
- Edit permissions for an app or add-on
- Enable or disable an app or add-on
- Perform actions, such as launch the app, edit the properties, and view app objects
Edit app and add-on properties
The edits you make to configuration and properties depend on whether you are the owner of the app or a user.
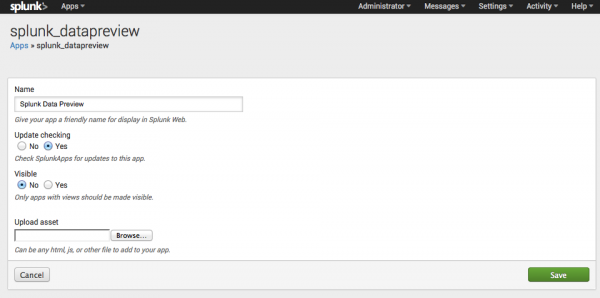
Select Apps > Manage Apps then click Edit properties for the app or add-on you want to edit. You can make the following edits for apps installed in this Splunk Enterprise instance.
- Name: Change the display name of the app or add-on in Splunk Web.
- Update checking: By default, update checking is enabled. You can override the default and disable update checking. See Checking for app an add-on updates below for details.
- Visible: Apps with views should be visible. Add-ons, which often do not have a view, should disable the visible property.
- Upload asset: Use this field to select a local file asset files, such as an HTML, JavaScript, or CSS file that can be accessed by the app or add-on. You can only upload one file at a time from this panel.
Refer to Develop Splunk apps for Splunk Cloud or Splunk Enterprise on the Splunk Developer Portal for details on the configuration and properties of apps and add-ons.
For a discussion of app object permissions, and governing access to those objects, see Set app permissions using Splunk Web on the Splunk Developer Portal.
Checking for updates
You can configure Splunk Enterprise to check Splunkbase for updates to an app or add-on. By default, checking for updates is enabled. You can disable checking for updates for an app by editing this property from Settings > Apps > Edit properties.
However, if this property is not available in Splunk Web, you can also manually edit the apps app.conf file to disable checking for updates. Create or edit the following stanza in $SPLUNK_HOME/etc/apps/<app_name>/local/app.conf to disable checking for updates:
[package] check_for_updates = 0
Note: Edit the local version of app.conf, not the default version. This avoids overriding your setting with the next update of the app.
| Manage app and add-on objects | Install SPL2-based apps |
This documentation applies to the following versions of Splunk® Enterprise: 7.0.0, 7.0.1, 7.0.2, 7.0.3, 7.0.4, 7.0.5, 7.0.6, 7.0.7, 7.0.8, 7.0.9, 7.0.10, 7.0.11, 7.0.13, 7.1.0, 7.1.1, 7.1.2, 7.1.3, 7.1.4, 7.1.5, 7.1.6, 7.1.7, 7.1.8, 7.1.9, 7.1.10, 7.2.0, 7.2.1, 7.2.2, 7.2.3, 7.2.4, 7.2.5, 7.2.6, 7.2.7, 7.2.8, 7.2.9, 7.2.10, 7.3.0, 7.3.1, 7.3.2, 7.3.3, 7.3.4, 7.3.5, 7.3.6, 7.3.7, 7.3.8, 7.3.9, 8.0.0, 8.0.1, 8.0.2, 8.0.3, 8.0.4, 8.0.5, 8.0.6, 8.0.7, 8.0.8, 8.0.9, 8.0.10, 8.1.0, 8.1.1, 8.1.2, 8.1.3, 8.1.4, 8.1.5, 8.1.6, 8.1.7, 8.1.8, 8.1.9, 8.1.10, 8.1.11, 8.1.12, 8.1.13, 8.1.14, 8.2.0, 8.2.1, 8.2.2, 8.2.3, 8.2.4, 8.2.5, 8.2.6, 8.2.7, 8.2.8, 8.2.9, 8.2.10, 8.2.11, 8.2.12, 9.0.0, 9.0.1, 9.0.2, 9.0.3, 9.0.4, 9.0.5, 9.0.6, 9.0.7, 9.0.8, 9.0.9, 9.0.10, 9.1.0, 9.1.1, 9.1.2, 9.1.3, 9.1.4, 9.1.5, 9.1.6, 9.1.7, 9.1.8, 9.1.9, 9.2.0, 9.2.1, 9.2.2, 9.2.3, 9.2.4, 9.2.5, 9.2.6, 9.3.0, 9.3.1, 9.3.2, 9.3.3, 9.3.4, 9.4.0, 9.4.1, 9.4.2
 Download manual
Download manual
Feedback submitted, thanks!