fieldsummary
Description
The fieldsummary command calculates summary statistics for all fields or a subset of the fields in your events. The summary information is displayed as a results table.
Syntax
fieldsummary [maxvals=<unsigned_int>] [<wc-field-list>]
Optional arguments
- maxvals
- Syntax: maxvals=<unsigned_int>
- Description: Specifies the maximum distinct values to return for each field. Cannot be negative. Set
maxvals = 0to return all available distinct values for each field. - Default: 100
- wc-field-list
- Syntax: <field> ...
- Description: A single field name or a space-delimited list of field names. You can use the asterisk ( * ) as a wildcard to specify a list of fields with similar names. For example, if you want to specify all fields that start with "value", you can use a wildcard such as
value*.
Usage
The fieldsummary command is a dataset processing command. See Command types.
The fieldsummary command displays the summary information in a results table. The following information appears in the results table:
| Summary field name | Description |
|---|---|
field
|
The field name in the event. |
count
|
The number of events/results with that field. |
distinct_count
|
The number of unique values in the field. |
is_exact
|
Whether or not the field is exact. This is related to the distinct count of the field values. If the number of values of the field exceeds maxvals, then fieldsummary will stop retaining all the values and compute an approximate distinct count instead of an exact one. 1 means it is exact, 0 means it is not.
|
max
|
If the field is numeric, the maximum of its value. |
mean
|
If the field is numeric, the mean of its values. |
min
|
If the field is numeric, the minimum of its values. |
numeric_count
|
The count of numeric values in the field. This would not include NULL values. |
stdev
|
If the field is numeric, the standard deviation of its values. |
values
|
The distinct values of the field and count of each value. The values are sorted first by highest count and then by distinct value, in ascending order. |
Examples
1. Return summaries for all fields
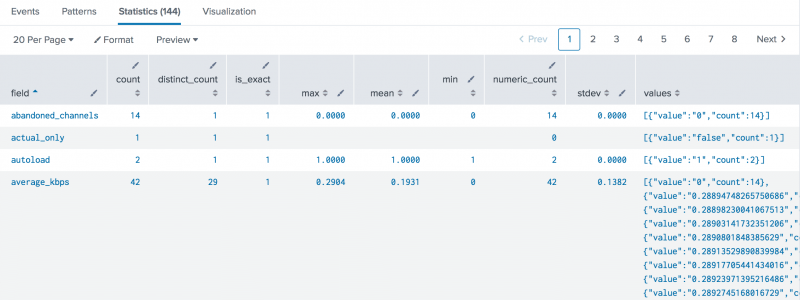
This example returns summaries for all fields in the _internal index from the last 15 minutes.
index=_internal earliest=-15m latest=now | fieldsummary
In this example, the results in the max, min, and stdev fields are formatted to display up to 4 decimal points.
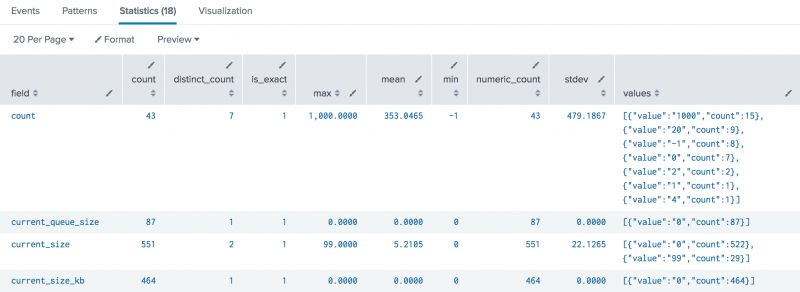
2. Return summaries for specific fields
This example returns summaries for fields in the _internal index with names that contain "size" and "count". The search returns only the top 10 values for each field from the last 15 minutes.
index=_internal earliest=-15m latest=now | fieldsummary maxvals=10 *size* *count*
See also
| fields | filldown |
This documentation applies to the following versions of Splunk® Enterprise: 7.1.0, 7.1.1, 7.1.2, 7.1.3, 7.1.4, 7.1.5, 7.1.6, 7.1.7, 7.1.8, 7.1.9, 7.1.10, 7.2.0, 7.2.1, 7.2.2, 7.2.3, 7.2.4, 7.2.5, 7.2.6, 7.2.7, 7.2.8, 7.2.9, 7.2.10, 7.3.0, 7.3.1, 7.3.2, 7.3.3, 7.3.4, 7.3.5, 7.3.6, 7.3.7, 7.3.8, 7.3.9, 8.0.0, 8.0.1, 8.0.2, 8.0.3, 8.0.4, 8.0.5, 8.0.6, 8.0.7, 8.0.8, 8.0.9, 8.0.10, 8.1.0, 8.1.1, 8.1.2, 8.1.3, 8.1.4, 8.1.5, 8.1.6, 8.1.7, 8.1.8, 8.1.9, 8.1.10, 8.1.11, 8.1.12, 8.1.13, 8.1.14, 8.2.0, 8.2.1, 8.2.2, 8.2.3, 8.2.4, 8.2.5, 8.2.6, 8.2.7, 8.2.8, 8.2.9, 8.2.10, 8.2.11, 8.2.12, 9.0.0, 9.0.1, 9.0.2, 9.0.3, 9.0.4, 9.0.5, 9.0.6, 9.0.7, 9.0.8, 9.0.9, 9.0.10, 9.1.0, 9.1.1, 9.1.2, 9.1.3, 9.1.4, 9.1.5, 9.1.6, 9.1.7, 9.1.8, 9.1.9, 9.2.0, 9.2.1, 9.2.2, 9.2.3, 9.2.4, 9.2.5, 9.2.6, 9.3.0, 9.3.1, 9.3.2, 9.3.3, 9.3.4, 9.4.0, 9.4.1, 9.4.2
 Download manual
Download manual
Feedback submitted, thanks!