Tag the host field
Tagging the host field is useful for knowledge capture and sharing, and for crafting more precise searches. You can tag the host field with one or more words. Use this to group hosts by function or type, to enable users to easily search for all activity on a group of similar servers. If you've changed the value of the host field for a given input, you can also tag events that are already in the index with the new host name to make it easier to search across your data set.
Add a tag to the host field in search results
You can add a tag to a host field-value combination in your search results.
Prerequisites
Steps
- Perform a search for data from the host you'd like to tag.
- In the search results, click on the arrow associated with the event containing the field you want to tag. In the expanded list, click on the arrow under Actions associated the field, then select Edit Tags.
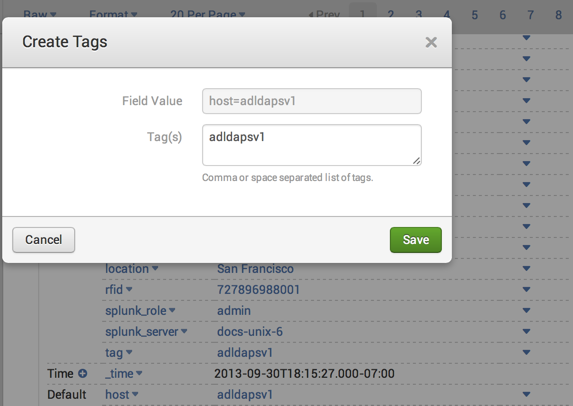
- In the Create Tags dialog enter the host field value that you'd like to tag, for example in Field Value enter Tag host= <current host value>. Enter your tag or tags, separated by commas or spaces, and click Save.
Host names vs. tagging the host field
The value of the host field is set when an event is indexed. It can be set by default based on the Splunk server hostname, set for a given input, or extracted from each event's data. Tagging the host field with an alternate hostname doesn't change the actual value of the host field, but it lets you search for the tag you specified instead of having to use the host field value. Each event can have only one host name, but multiple host tags.
For example, if your Splunk server is receiving compliance data from a specific host, tagging that host with compliance will help your compliance searches. With host tags, you can create a loose grouping of data without masking or changing the underlying host name.
You might also want to tag the host field with another host name if you indexed some data from a particular input source and then decided to change the value of the host field for that input--all the new data coming in from that input will have the new host field value, but the data that already exists in your index will have the old value. Tagging the host field for the existing data lets you search for the new host value without excluding all the existing data.
| Define and manage tags in Settings | Tag event types |
This documentation applies to the following versions of Splunk Cloud Platform™: 9.3.2411 (latest FedRAMP release), 8.2.2112, 8.2.2201, 8.2.2203, 8.2.2202, 9.0.2205, 9.0.2208, 9.0.2209, 9.0.2303, 9.0.2305, 9.1.2308, 9.1.2312, 9.2.2403, 9.2.2406, 9.3.2408
 Download manual
Download manual
Feedback submitted, thanks!