How urgency is assigned to notable events in Splunk Enterprise Security
The urgency_lookup determines the urgency level by using both the severity and priority value assigned to the notable that is generated from the correlation search and the priority assigned to specific fields in the assets and identities.
The following fields are used to determine priority when priority is assigned through an asset and identity lookup:
- For identities:
userorsrc_user - For assets:
dest,src, ordvc
The severity value is set directly on the notable that is generated by the correlation search. If both the asset and identity in the notable event have an assigned priority, the higher priority is used to calculate the urgency. You may use the Urgency field to prioritize the investigation of notable events.
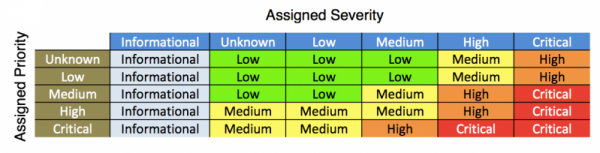
This table provides an example of how the urgency values are calculated in notable events by default. The default results can be overwritten by modifying priority and rank, search syntax, or urgency lookups.
- If event severity is informational, the event urgency is informational, regardless of asset priority.
- If asset priority is unknown or low and event severity is unknown, low, or medium, the event urgency is low.
- If asset priority is unknown or low and event severity is high, the event urgency is medium.
- If asset priority is unknown or low and event severity is critical, the event urgency is high.
- If asset priority is unknown or low and event severity is critical, the event urgency is high.
- If asset priority is medium and event severity is unknown or low, the event urgency is low.
- If asset priority is medium and event severity is medium, the event urgency is medium.
- If asset priority is medium and event severity is high, the event urgency is high.
- If asset priority is medium and event severity is critical, the event urgency is critical.
- If asset priority is high and event severity is unknown, low, or medium, the event urgency is medium.
- If asset priority is medium and event severity is high, the event urgency is high.
- If asset priority is medium and event severity is critical, the event urgency is critical.
- If asset priority is critical and event severity is unknown or low, the event urgency is medium.
- If asset priority is critical and event severity is medium, the event urgency is high.
- If asset priority is critical and event severity is high or critical, the event urgency is critical.
A notable event can be assigned an "unknown" urgency level if the priority value from the asset and identity lookups or the severity value assigned by the correlation search or in a triggering event is not recognized by Enterprise Security.
Incident Review filters on the urgencies of "high", "medium", "low", "critical", "informational", or "unknown." Any value that is not one of the filtered urgencies also defaults to "unknown". This ensures that all notable events are displayed in Incident Review.
You may also modify the urgency level once the notable is created and this modified value for urgency is then used by the incident review lookup.
Modify notable event urgency
Use one of the following methods to modify the urgency assigned to notable events:
- Modify priority and rank in the Asset and Identity Framework
- Modify notable event severity in correlation search syntax
- Modify the urgency lookup directly
Modify priority and rank in the Asset and Identity Framework
When asset and identity correlation is enabled, if you have made your lookups automatic, the Asset and Identity Framework helps to calculate the event urgency. When a correlation search runs, the results are enriched with the data from these automatic lookups. The priority field in an automatic lookup table affects notable event urgency. See Correlation Setup for enabling correlation and making lookups automatic.
You can rank the order of your asset and identity lists to determine priority for merging assets and identities. For example, if you have identity lists called source A and source B:
| Source A | Source B |
|---|---|
|
|
These merge on the matching key identity fields, and the priority is set to low. Source A is the higher rank, therefore takes higher precedence when merging single valued fields. If two or more sources have the same rank, then the last nonempty value is the priority. See Rank the order for merging assets and Rank the order for merging identities for merge ranking.
See Search preview for testing the merge to collections.
The data is merged into three different collections: asset_lookup_by_str, asset_lookup_by_cidr, and identities_lookup_expanded. Lookups on these collections are based on a primary key. Therefore, an event is typically not enriched by both an asset and an identity collection. However, if it does happen, then a field such as priority would be displayed depending on its alias as defined in props.conf. If there is an event that is enriched by both asset and identity lookups, then the event has the fields dest_priority, dvc_priority, and src_priority (coming from asset enrichment) and src_user_priority and user_priority (coming from identity enrichment).
See Reset collections to reset the collections.
Modify notable event severity in correlation search syntax
Potentially modify the urgency of a notable event by defining severity in the correlation search syntax. You must have access to edit correlation searches to make these changes.
For example, if you want to change the severity of a correlation search according to the number of failures in the search results. To set a "critical" severity when there are more than 100 failures, a high severity when there are more than 50 failures, and a medium severity for the rest of the results, add search syntax like the following example to the end of the correlation search:
... | eval severity=case(failure>100,"critical",failure>50,"high",failure<=50,"medium")
Severity defined in the search syntax results in an event where severity takes precedence over the severity defined in the notable event adaptive response action.
Modify the urgency lookup directly
You can change which severity and priority values result in which calculated urgency values for notable events in Splunk Enterprise Security.
Only specific values are valid for severity or priority values. Use only those values when modifying the lookup. Do not modify the names of the notable event urgency values.
- Valid severity values: unknown, informational, low, medium, high, critical.
- Valid priority values: unknown, low, medium, high, critical.
- Valid urgency values: informational, low, medium, high, critical.
- On the Enterprise Security menu bar, select Configure > Content > Content Management.
- Choose the Urgency Levels lookup. An editable, color coded table representing the urgency lookup file displays.
- In any row where the priority or severity is listed as unknown, review the assigned urgency.
- (Optional) Edit the table and change the urgency to another one of the accepted values. All urgency values must be lower case.
- Click Save.
| Included adaptive response actions with | Investigations in |
This documentation applies to the following versions of Splunk® Enterprise Security: 7.0.1, 7.0.2, 7.1.0, 7.1.1, 7.1.2, 7.2.0, 7.3.0, 7.3.1, 7.3.2
 Download manual
Download manual
Feedback submitted, thanks!