Manage security investigations in
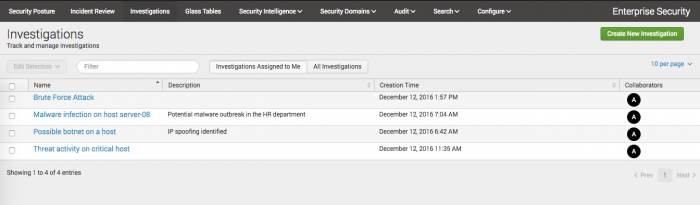
You can manage, start, and track investigations on the Investigations dashboard. View or filter the investigations assigned to you, or create one. You can view all investigations that you collaborate on using this dashboard. Users with admin permissions can also view all investigations that exist in Splunk Enterprise Security.
By default, analysts that use this page only see investigations assigned to them unless they also have the capability to manage all investigations.
Manage your investigations
Manage ongoing investigations from the Investigations dashboard. You can see the titles, descriptions, creation times, and collaborators on the investigations assigned to you or on all investigations in .
Filter investigations
Quickly find an investigation or refine the list of investigations by filtering. Type in the Filter box to search the title and description fields of investigations.
Delete investigations
You can delete individual or several investigations on the Investigations dashboard. After you delete a timeline, you cannot restore it. Assess the audit or research value of a timeline before deleting it.
- Select the check box next to the investigation or investigations you want to delete.
- Click Edit Selection and click Delete.
- Click Delete to confirm deleting the timeline.
Edit an investigation
Edit the title or description of an investigation by opening the investigation. Only collaborators with write permissions on an investigation can make changes to an investigation.
- Find the investigation you want to edit on the Investigations dashboard.
- Click the name of the investigation to open it.
See Create and track investigations in Splunk Enterprise Security.
Data sources for investigations
stores investigation information in several KVStore collections. The investigations on the Investigations dashboard, items added to the investigation, and attachments added to the investigation each have their own collection. See Investigations in the Dashboard requirements matrix.
Investigation details from investigations created in pre-4.6.0 versions of Splunk Enterprise Security are stored in two KV Store collections: investigative_canvas, investigative_canvas_entries. Those collections are preserved in version 4.6.0 but the contents are added to the new investigation KV Store collections.
Action history data sources
Action history items do not immediately appear in your action history after you perform an action. You can only view action history items and add them to an investigation after the saved searches that create action history items run. By default, the searches run every two minutes. Five saved searches create action history items.
- Dashboard Views - Action History
- Search Tracking - Action History
- Per-Panel Filtering - Action History
- Notable Suppression - Action History
- Notable Status - Action History
View the searches by navigating to Configure > Content Management and using the filters on the page. If you change these saved searches, action history items might stop appearing in your action history. To exclude a search from your action history, use the Action History Search Tracking Whitelist lookup. See Configure lists and lookups.
Access to investigations
Users with the ess_admin role can create, view, and manage investigations by default. Users with the ess_analyst role can create and edit investigations. Make changes to capabilities with the Permissions dashboard.
- To allow other users to create or edit an investigation, add the Use Investigations capability to their role. Users can only make changes on investigations on which they are a collaborator.
- To allow other users to manage, view, and delete all investigations, add the Manage all investigations capability to their role.
See Configure users and and roles in the Installation and Upgrade Manual.
You can manage who can make changes to an investigation by setting write permissions for collaborators on a specific investigation. By default, all collaborators have write permissions for the investigations to which they are added, but other collaborators on the timeline can change those permissions to read-only. See Make changes to the collaborators on an investigation.
After a user creates an investigation, any user with the Manage all investigations capability can view the investigation, but only the collaborators on the investigation can edit the investigation. You cannot view the investigation KV Store collections as lookups.
| Create and track investigations in | Asset and Identity dashboards |
This documentation applies to the following versions of Splunk® Enterprise Security: 4.6.0 Cloud only
 Download manual
Download manual
Feedback submitted, thanks!