Isolate threats with risk alerting
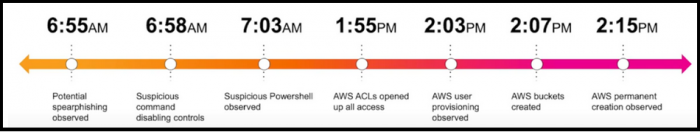
Buttercup Games, a fictitious company, runs an e-commerce site to sell its products. Kay, the manager of the security operations center (SOC) at Buttercup Games, receives numerous notables during the course of a morning indicating various suspicious behaviors over a specific time period that may be a risk to his organization.
Previously, Kay requested Ram, a security analyst on his team, to use Splunk Enterprise Security to run correlation searches on all assets and identities to generate security events and create notables or risk alerts. However, correlation searches generated an excessive amount of notables and manually parsing through them to identify patterns was neither efficient nor effective for detecting security threats to Buttercup Games on time. High-fidelity notables were often suppressed and didn't get incorporated into the investigative story, creating visibility gaps.
This time, Kay asks Ram to use the risk alerting framework in Splunk Enterprise Security to dynamically adjust risk scores for assets and identities based on specific conditions. Dynamically adjusting risk scores allows Ram to automatically raise the risk scores associated with specific assets and identities by assigning these conditions as risk factors. Assigning risk factors helps to expose notables earlier for investigation. Therefore, Ram can prioritize suspicious behavior and mitigate risk by taking quick action on the risk event.
The risk alerting framework in Splunk Enterprise Security allows Kay and Ram to conduct higher value investigations through more streamlined and effective threat isolation. Ram leverages the risk alerting framework to explore the high volume and noisy endpoint data that Kay asked him to investigate. This use case describes how Kay, a SOC manager, and Ram, a security analyst, use risk scores and risk factoring to classify the notables based on risk level and map out the risk in their security environment by taking these steps.
- Assign risk scores to assets and identities
- Generate notables using correlation searches
- Add annotations to enrich correlation search results
- Classify risk objects based on annotations
- Add a risk message and a risk score to a notable
- Adjust risk scores for specific objects
See also
This documentation applies to the following versions of Splunk® Enterprise Security: 7.0.1, 7.0.2, 7.1.0, 7.1.1, 7.2.0
 Download manual
Download manual
Feedback submitted, thanks!