Add details to an investigation in
As an analyst working on an investigation, add details and evidence to your investigation by adding events, actions, and notes. While you conduct your investigation using , you can add notable events or Splunk events that add insight to the investigation. Add searches, suppression filters, and dashboard views to the investigation from your action history. Record important investigation steps that you take, such as phone, email, or chat conversations as notes on the investigation. You can use notes to add relevant information like links to online press coverage, tweets, or upload screenshots and files.
Run a quick search from the investigation bar
Run a search without opening the search dashboard by clicking Quick Search ![]() on the investigation bar.
on the investigation bar.
- Add the search to the investigation in the investigation bar by clicking Add to Investigation.
- Use the Event Actions to add specific events in the search results to an investigation.
- To save the search results at investigation time, click Export to export the search results as a CSV file. Add the search results as an attachment to a note on the investigation.
- Click Open in Search to view the search results on the Search dashboard.
- Enlarge or shrink your view of the search results by clicking and dragging the corner of the window. Double click to expand the search view to cover most of your screen, or double click again to shrink it.
Add a notable event to an investigation
You can add a notable event to an investigation from the Incident Review dashboard. See Add a notable event to an investigation.
If the status of a notable event changes, or if an adaptive response action is run from the notable event, the investigation is updated with that information.
Add a Splunk event to an investigation
Add an event from the Splunk search page to an investigation. You can only add an event to an investigation from the search page in the Splunk App for PCI Compliance context.
- Expand the event details to see the Event Actions menu and other information.
- Click Event Actions and select Add to Investigation.
- A tab opens. Select from existing investigations, or create one.
- Click Save.
Add an entry from your action history to an investigation
The action history stores a history of the actions that you have performed in , such as searches that you have run, dashboards you have viewed, and per-panel filtering actions that you have performed.
Add an entry to an investigation from your action history with the investigation bar. Search for specific types of action history items over time to find the action history items that you want to add to your investigation.
- From the investigation bar, click the
 icon.
icon. - Select an action history type and optionally change the time range.
- Click Search to retrieve a list of action history items.
- Find the actions that you want to add to the investigation. For example, view the dashboards that you viewed to add them to your investigation.
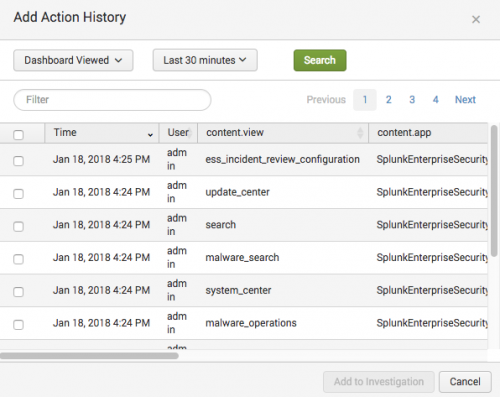
- The actions that you've taken display in the action history dialog box. You can only add actions from your own action history.
- Locate the action you want to add and select the check box next to the action or actions that you want to add to the investigation timeline.
- Click Add to Investigation.
The actions are added to the investigation that you are viewing or that is selected in the investigation bar.
See Refer to your action history.
Add a note to an investigation
Add a note to an investigation to record investigation details or add attachments. You can add a note from dashboards in .
- From the investigation bar, click the
 icon.
icon. - Type a title.
For example, "Phone conversation with police." - (Optional) Select a time. The default is the current date and time.
For example, select the time of the phone call. - (Optional) Type a description.
For example, a note to record a phone conversation might include the description: Called the police. Spoke with Detective Reggie Martin. Discussed an employee stealing identities from other employees.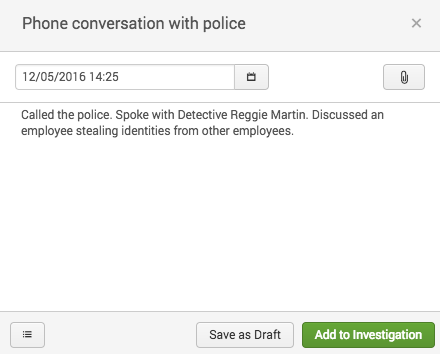
- (Optional): Attach a file to the note.
- Click Add to Investigation to add the note to the open investigation or click Save as Draft.
When you save a note as a draft, it stays associated with the investigation that was selected when you created the note but does not appear on the investigation. Retrieve draft notes by clicking the ![]() icon.
icon. 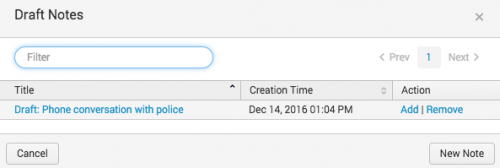
| Investigate a potential security incident on the investigation workbench in the | Make changes to an investigation in |
This documentation applies to the following versions of Splunk® App for PCI Compliance: 5.0.1, 5.0.2, 5.1.0, 5.1.1, 5.1.2, 5.2.0, 5.3.0, 5.3.1, 5.3.2, 5.3.3, 6.1.0
 Download manual
Download manual
Feedback submitted, thanks!