About the Splunk Phantom Add-on for Splunk
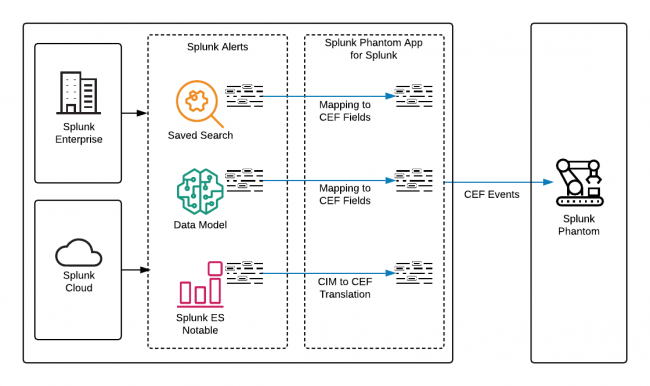
Splunk Phantom can use the Splunk platform as a source of data by ingesting events. The Splunk Phantom App for Splunk is required to configure Splunk Enterprise or Splunk Cloud as a data source for Splunk Phantom.
The Splunk Phantom App for Splunk is installed as an app on the Splunk platform and forwards events to Splunk Phantom. The Splunk platform environment consists of raw events or Common Information Model (CIM) data, while Splunk Phantom uses the Common Event Format (CEF). The Splunk Phantom App for Splunk acts as a translation service between the Splunk platform and Splunk Phantom by performing the following tasks:
- Mapping fields from Splunk platform alerts, such as saved searches and data models, to CEF fields.
- Translating CIM fields from Splunk Enterprise Security (ES) notables to CEF fields.
- Forwarding events in CEF format to Splunk Phantom, which are stored as artifacts.
| Differences between data models and saved searches |
This documentation applies to the following versions of Splunk® Phantom App for Splunk: 2.7.5, 3.0.5, 4.0.10, 4.0.35
 Download manual
Download manual
Feedback submitted, thanks!