Set up remote search on a distributed Splunk Enterprise instance or Splunk Cloud Platform instance
If you are using Splunk SOAR version 6.2.0 or higher, use the universal forwarder. See Set up universal forwarder using Splunk SOAR version 6.2.0 or higher.
This article is for Splunk Cloud Platform instances or distributed Splunk Enterprise instances only. For standalone Splunk Enterprise instances, see Set up remote search on a standalone Splunk Enterprise instance.
This article describes logs for data within Splunk SOAR. For information on logs for the system where Splunk SOAR is installed, see Configure SOAR system logs using Splunk App for SOAR.
This is an overview of the steps needed to connect your Splunk SOAR instance or cluster to a distributed Splunk Cloud Platform or Enterprise instance. Steps here link to detailed steps later in this article.
- Before you begin
- Set up the HTTP Event Collector on the distributed Splunk Cloud Platform or Splunk Enterprise instance.
- Configure Splunk SOAR to use a Splunk Cloud Platform or distributed Splunk Enterprise deployment.
Before you begin
Before you begin, make sure that you have completed the following tasks, described in Assign roles for Splunk App for SOAR:
- Assign the required roles
- Create the required user accounts for Splunk SOAR
Set up the HTTP Event Collector on the distributed Splunk Cloud Platform or Splunk Enterprise instance
Enable the HTTP Event Collector (HEC) on Splunk Cloud Platform or Splunk Enterprise and create a new token so you can use the HEC. Repeat these tasks on other indexers if those other indexers require separate HEC tokens. See Scale HTTP Event Collector with distributed deployments in the Splunk Enterprise Getting Data In manual for more information.
Follow the instructions for your Splunk Cloud Platform or Splunk Enterprise instance:
| Deployment Type | Documentation |
|---|---|
| Distributed Splunk Enterprise | See Configure HTTP Event Collector on Splunk Enterprise in the Splunk Enterprise Getting Data In manual for instructions. |
| Splunk Cloud Platform | See Configure HTTP Event Collector on Splunk Cloud in the Splunk Enterprise Getting Data In manual for instructions. |
| Splunk Cloud Platform free trial | See Configure HTTP Event Collector on Splunk Cloud free trial in the Splunk Enterprise Getting Data In manual for instructions. |
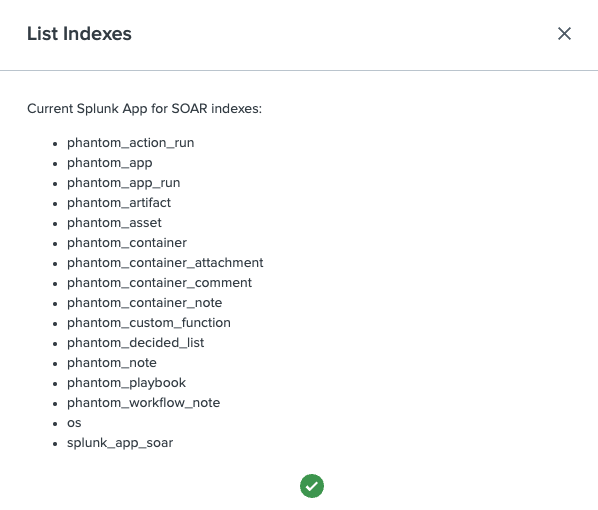
When you are creating the new token, add all the indexes listed below, including any custom indexes, and move them to the Selected item(s) list. Then, select the index you want to use as the default index, such as phantom_app. The following screenshot shows an example.
The following is a list of all the Splunk SOAR indexes available for the HTTP Event Collector:
- phantom_action_run
- phantom_app
- phantom_app_run
- phantom_artifact
- phantom_asset
- phantom_container
- phantom_container_attachment
- phantom_container_comment
- phantom_custom_function
- phantom_decided_list
- phantom_note
- phantom_playbook
- os
- splunk_app_soar
On the HTTP Event Collector page, copy the token value for the new token. You will need this value when you configure Splunk SOAR. If you don't copy it now, you can return to the HTTP Event Collector page to obtain the value later when you need it.
Using custom prefixes
If you have multiple Splunk SOAR instances in your environment, you can append a custom prefix to the index created on Splunk Cloud Platform or Enterprise. Use the custom prefix to create separate indexes for each Splunk SOAR instance, which provides data separation and the ability to correlate each index with the appropriate Splunk SOAR instance. For more information, see Define a custom index per Splunk SOAR instance.
If you want to define a custom prefix, the admin user defined in this command must also be assigned the splunk_app_soar role:
phenv set_preference --splunk-index-prefix="<prefixstring>" --splunk-admin-username <splunkadminusername>
Restart Splunk if your Splunk SOAR indexes are not recognized
In some cases, Splunk Cloud Platform does not recognize Splunk SOAR indexes, in which case data such as the custom function data won't be indexed. You will see an error like the following example in your Splunk logs:
03-15-2021 19:10:07.802 +0000 WARN IndexAdminHandler [23800 TcpChannelThread] - idx=newsearch_phantom_custom_function Unable to reload indexer after adding: reason='already reloading or shutting down, will not reload'. Restart required.
Restart your Splunk Cloud Platform instance to resolve this issue.
Configure Splunk SOAR to use a Splunk Cloud Platform or distributed Splunk Enterprise deployment
After the remote search service is installed and the required user accounts are created, configure Splunk SOAR to use a distributed Splunk Cloud Platform or Splunk Enterprise deployment.
Required search head information
Verify that you have the following search head information:
- The host names for each search head. For Splunk Cloud Platform, use the name of your search head stack, which looks like
<deployment name>.splunkcloud.com. Do not includehttps://. - The user names and passwords for the user accounts with the
phantomsearchandphantomdeleteroles. - The REST API port numbers for each search head.
When using the Input Data Manager, the HEC token must be generated from the main search head which is the ad-hoc search head in in Splunk Cloud Platform deployments.
Managed Splunk Cloud Platform users must open a support case to open the REST API port for Splunk Cloud Platform. Include a range of IP addresses to authorize access to the REST API from your organization. See How do I file a Splunk Support Case/contact Splunk Support? on Splunk Answers.
Required indexer information
Verify that you have the following indexer information:
- Host names for each indexer. For Splunk Cloud Platform, use the
http-inputsprefix for your deployment, which looks likehttp-inputs-<deployment name>.splunkcloud.com. - The HTTP Event Collector port number. The default port is 8088 for HTTP traffic or 443 for HTTPS traffic. Splunk Cloud Platform requires HTTPS.
- The HTTP Event Collector token.
If your indexers are configured behind a load balancer, use the load balancer URL for the indexer host name.
Add search head and indexers
You can add up to 10 search heads and 10 indexers.
- Log in to Splunk SOAR as an administrative user.
- From the main menu, select Administration.
- Select Administration Settings.
- Select Search Settings.
- In the Search Endpoint field, select the radio button for Distributed Splunk Enterprise Deployment.
- Select Search Heads.
- Select Host to expand the Search Heads configuration.
- In the Search Heads section, configure the first search head.
- Type the search head host name in the Host field.
- In the User with Search Privileges section, type the user name and password for the user account with the
phantomsearch role in the Username and Password fields. - In the User with Delete Privileges section, type the user name and password for the user account with the
phantomdeleterole in the Username and Password fields. - Type the port number that the Splunk platform uses to listen for REST API calls in the REST Port field.
- Check the Use SSL for REST box to enable SSL.
- Check the Verify Certificate for REST box to enable SSL certificate verification.
- Select Add Search Head to configure additional search heads. Each time you add a new search head, the user names and passwords for the user accounts with the
phantomsearchandphantomdeleteroles are prepopulated using the values from the previous search head. - Once all the search heads have been added, select Indexers.
- Select Host to expand the Indexers configuration.
- In the Indexers section, configure the first indexer.
- Enter the indexer host name in the Host field.
- Enter the HTTP Event Collector port in the HTTP Event Collector Port field.
- Paste the HTTP Event Collector token in the HTTP Event Collector Token field.
- Check the Use SSL for HTTP Event Collector box to enable SSL.
- Check the Verify Certificate for HTTP Event Collector box to enable SSL certificate verification.
- Select Add Indexer to configure additional indexers.
- Once all search heads and indexers have been added, test the connections to your distributed Splunk platform deployment by selecting Test Connection.
- Select Save Changes.
| Set up remote search on a standalone Splunk Enterprise instance | Modify srchDiskQuota |
This documentation applies to the following versions of Splunk® App for SOAR: 1.0.0, 1.0.38, 1.0.41, 1.0.57, 1.0.67, 1.0.71
 Download manual
Download manual
Feedback submitted, thanks!