Change default values
Before you begin configuring Splunk Enterprise for your environment, review the following default settings.
Set or change environment variables
Use operating system environment variables to modify specific default values for the Splunk Enterprise services.
- On *nix, use the
setenvorexportcommands to set a particular variable. For example:To modify the environment permanently, edit your shell initialization file, and add entries for the variables you want Splunk Enterprise to use when it starts up.# export SPLUNK_HOME = /opt/splunk02/splunk
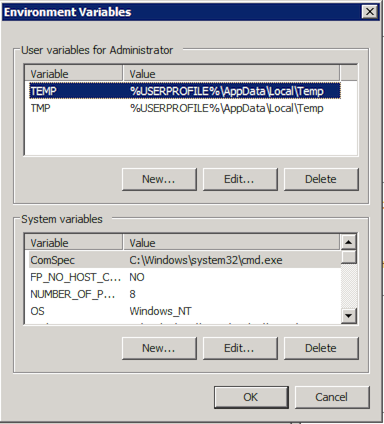
- On Windows, use the
setenvironment variable in either a command prompt or PowerShell window:To set the environment permanently, use the "Environment Variables" window, and add an entry to the "User variables" list.C:\> set SPLUNK_HOME = "C:\Program Files\Splunk"
Several environment variables are available:
| Environment variable | Purpose |
|---|---|
SPLUNK_HOME
|
The fully qualified path to the Splunk Enterprise installation directory. |
SPLUNK_DB
|
The fully qualified path to the root directory that contains the Splunk Enterprise indexes. |
SPLUNK_BINDIP
|
The host IP address that Splunk Enterprise should bind to on startup. On hosts with multiple IP addresses, this is used to limit accepted connections to one IP address. |
SPLUNK_OS_USER
|
Tells Splunk Enterprise to assume the credentials of the user you specify, regardless of what user you started it as. For example, if you specify the SPLUNK_OS_USER 'splunk' but start Splunk Enterprise as root, the system adopts the privileges of the 'splunk' user, and any files written by those processes will be owned by the 'splunk' user.
|
SPLUNK_SERVER_NAME
|
The name of the splunkd service (on Windows) or process (on *nix). Do not set this variable unless you know what you are doing. |
SPLUNK_WEB_NAME
|
The name of the splunkweb service (on Windows) or process (on *nix). Do not set this variable unless you know what you are doing. |
Note: You can set these environment variables in the splunk-launch.conf or web.conf file. This is useful when you run more than one Splunk software instance on a host. See splunk-launch.conf.
Change network ports
Splunk Enterprise configures default TCP ports during installation:
- The HTTP/HTTPS port. This port provides the socket for Splunk Web. It defaults to 8000.
- The appserver port. 8065 by default.
- The management port. This port is used to communicate with the splunkd daemon. Splunk Web talks to splunkd on this port, as does the command line interface, and any distributed connections from other servers. This port defaults to 8089.
- The KV store port. 8191 by default.
The default network ports are recommendations, and might not represent what your Splunk Enterprise instance is using. During the Splunk Enterprise installation, if any default port is detected as in-use, you are prompted to provide alternative port assignments.
Splunk instances that are receiving data from forwarders must be configured with a receiver port. The receiver port only listens for incoming data from forwarders. Configuration of the receiver port does not occur during installation. For more information, see Enable a receiver in the Forwarding Data Manual.
Use Splunk Web
To change the ports from their installation settings:
- Log into Splunk Web as the admin user.
- Click Settings.
- Click Server settings.
- Click General settings.
- Change the value for either Management port or Web port, and click Save.
Use Splunk CLI
To change the port settings using the Splunk CLI, use the CLI command set. For example, this sets the Splunk Web port to 9000:
splunk set web-port 9000
This command sets the splunkd port to 9089:
splunk set splunkd-port 9089
Change the default Splunk server name
The Splunk server name setting controls both the name that is displayed within Splunk Web, and the name that is sent to other Splunk Servers in a distributed deployment. The name is chosen from either the DNS or IP address of the Splunk Server host by default.
Use Splunk Web
To change the Splunk server name:
- Log into Splunk Web as the admin user.
- Click Settings.
- Click Server settings.
- Click General settings.
- Change the value for Splunk server name, and click Save.
Use Splunk CLI
To change the server name using the CLI, use the set servername command. For example, this sets the server name to foo:
splunk set servername foo
Set minimum free disk space
The minimum free disk space setting controls how low storage space in the datastore location can fall before Splunk software stops indexing. Splunk software resumes indexing when available space exceeds this threshold.
Use Splunk Web
To set minimum free storage space:
- Log into Splunk Web as the admin user.
- Click Settings.
- Click Server settings.
- Click General settings.
- Change the value for Pause indexing if free disk space (in MB) falls below, and click Save.
Use Splunk CLI
To change the minimum free space value using the CLI, use the set minfreemb command. For example, this sets the minimum free space to 2000 MB:
splunk set minfreemb 2000
Set the default time range
The default time range for ad hoc searches in the Search & Reporting App is set to Last 24 hours. A Splunk Enterprise administrator can set the default time range globally, across all apps. Splunk Cloud Platform customers cannot configure this setting directly. The setting is stored in $SPLUNK_HOME/etc/apps/user-prefs/local/user-prefs.conf file in the [general_default] stanza.
This setting applies to all Search pages in Splunk Apps, not only the Search & Reporting App. This setting applies to all user roles.
This setting does not apply to dashboards.
Use Splunk Web
- Log into Splunk Web as the admin user.
- Click Settings.
- Click Server settings.
- Click Search Preferences.
- From the Default search time range drop-down, select the time that you want to use and click Save.
Time range settings in the ui-prefs.conf file
You might already have a time range setting defined in the ui-prefs.conf file for a specific application or user. The settings in the ui-prefs.conf file take precedence over any settings that you make to the global default time range using Splunk Web.
However, if you want to use the global default time range for all users and applications, consider removing the settings that you have in the ui-prefs.conf file. See ui-prefs.conf.
Other default settings
The Settings screen offers additional pages with default settings for you to change. Explore the screen to see the range of options.
| Install your license | Bind Splunk to an IP |
This documentation applies to the following versions of Splunk® Enterprise: 7.1.0, 7.1.1, 7.1.2, 7.1.3, 7.1.4, 7.1.5, 7.1.6, 7.1.7, 7.1.8, 7.1.9, 7.1.10, 7.2.0, 7.2.1, 7.2.2, 7.2.3, 7.2.4, 7.2.5, 7.2.6, 7.2.7, 7.2.8, 7.2.9, 7.2.10, 7.3.0, 7.3.1, 7.3.2, 7.3.3, 7.3.4, 7.3.5, 7.3.6, 7.3.7, 7.3.8, 7.3.9, 8.0.0, 8.0.1, 8.0.2, 8.0.3, 8.0.4, 8.0.5, 8.0.6, 8.0.7, 8.0.8, 8.0.9, 8.0.10, 8.1.0, 8.1.1, 8.1.2, 8.1.3, 8.1.4, 8.1.5, 8.1.6, 8.1.7, 8.1.8, 8.1.9, 8.1.10, 8.1.11, 8.1.12, 8.1.13, 8.1.14, 8.2.0, 8.2.1, 8.2.2, 8.2.3, 8.2.4, 8.2.5, 8.2.6, 8.2.7, 8.2.8, 8.2.9, 8.2.10, 8.2.11, 8.2.12, 9.0.0, 9.0.1, 9.0.2, 9.0.3, 9.0.4, 9.0.5, 9.0.6, 9.0.7, 9.0.8, 9.0.9, 9.0.10, 9.1.0, 9.1.1, 9.1.2, 9.1.3, 9.1.4, 9.1.5, 9.1.6, 9.1.7, 9.1.8, 9.1.9, 9.2.0, 9.2.1, 9.2.2, 9.2.3, 9.2.4, 9.2.5, 9.2.6, 9.3.0, 9.3.1, 9.3.2, 9.3.3, 9.3.4, 9.4.0, 9.4.1, 9.4.2
 Download manual
Download manual
Feedback submitted, thanks!