About private connectivity
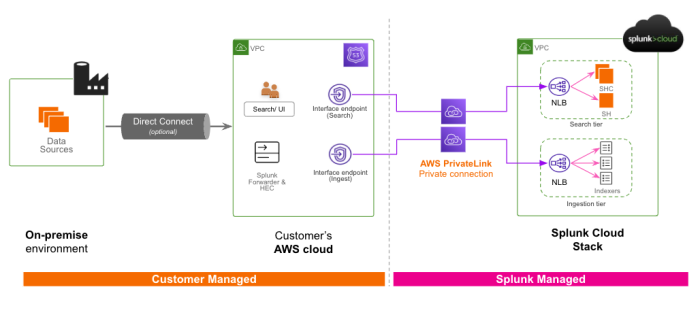
Splunk Cloud Platform private connectivity allows you to directly connect your Splunk Cloud Platform environment with your Amazon Virtual Private Cloud (VPC). This allows you to route the data for ingestion and search traffic into the Splunk Cloud Platform through the Amazon Web Service (AWS) internal network using AWS PrivateLink. Although AWS-to-AWS traffic should not leave the global AWS network (with a minor documented exception), the PrivateLink feature helps ensure that your AWS traffic sent to the Splunk Cloud Platform only traverses private IPs (in other words, non-public internet routable addresses).
Splunk Cloud Platform encrypts all data in flight by employing Transport Layer Security (TLS) 1.2+ for ingest data and Hypertext Transfer Protocol Secure (HTTPS) for search data. You can also restrict traffic further by establishing firewall rules or by creating an IP allow list. While these protections are sufficient for most Splunk Cloud Platform customers, Splunk Cloud Platform private connectivity supports the additional needs of customers for whom encrypting data in flight is insufficient to meet their organization's security and compliance requirements.
To configure private connectivity, Splunk Cloud Platform administrators can use Admin Config Service (ACS) APIs to confirm their eligibility and enable this feature. Splunk Cloud Platform will then provision service endpoints so that your data is accepted in your Splunk Cloud Platform deployment.
Requirements
To leverage private connectivity for your Splunk Cloud Platform deployment:
- You must be using AWS infrastructure.
- You must be on the Victoria Experience for AWS standard regions or the Classic Experience for USGov and FedRAMP Moderate regions.
- Your deployment must have one or more separate search heads or a search head cluster. Private connectivity requires ACS and ACS is not supported on single instance deployments.
- You must have
sc_adminrole for the ACS API.
Scope and considerations
Consider the following before enabling the private connectivity feature:
- Data that you send to the Splunk Cloud Platform from a universal forwarder, heavy forwarder, or HTTP Event Collector (HEC) for ingest into Splunk Cloud Platform will flow over AWS PrivateLink.
- Search, API and UI access traffic to Splunk Cloud Platform can be enabled to flow over AWS PrivateLink.
- AWS PrivateLink supports unidirectional data traversal only. Communication other than your AWS environment to Splunk Cloud Platform traffic will continue to flow using the public internet.
- All data other than searches and data sent for ingestion to Splunk Cloud Platform from an AWS environment (for example, Inputs Data Manager data, cloud to Splunk Enterprise Federated Search, and so on) will continue to use the public internet. This includes app data or services that require HTTP Event Collector (HEC) acknowledgements.
- Data that you send to the Splunk Cloud Platform must originate from the same region as your Splunk Cloud environment.
- To connect multiple AWS accounts through private connectivity, you need to create a VPC and PrivateLink endpoint for each account.
- You are responsible for AWS costs associated with your VPC. For more information, see: AWS PrivateLink pricing.
| Area | Customer Responsibilities | Splunk Responsibilities |
|---|---|---|
| Pre-enablement verification | Review and acknowledge the feature scope, consider security and implementation impact, align internal stakeholders, and prepare your environment for enablement. | N/A |
| Enablement | Follow Enable private connectivity to configure your Splunk Cloud Platform environment. | Provision service endpoints. |
| Network connectivity | For each connecting VPC, establish private endpoints and the appropriate DNS mappings for routing data using the AWS PrivateLink endpoint service.
For data ingest: Update universal forwarder credentials. (Optional) Search tier with SAML: Appropriate DNS routing to redirect SAML traffic via the internet and AWS PrivateLink. |
Accept data from private endpoints into the Splunk Cloud Platform. |
| Management | Configure resources like security group rules and DNS zones within your VPC and ensure service availability of those resources. | Maintain performance and availability standards defined in the Splunk Cloud Platform Service Level Agreement (SLA). |
If private connectivity meets your requirements, and you would like to enable this feature for your Splunk Cloud Platform deployment, follow the instructions in Enable private connectivity.
| Turn off Splunk platform field filters | Enable private connectivity |
This documentation applies to the following versions of Splunk Cloud Platform™: 9.0.2209, 9.0.2303, 9.0.2305, 9.1.2308, 9.1.2312, 9.2.2403, 9.2.2406, 9.3.2408, 9.3.2411 (latest FedRAMP release)
 Download manual
Download manual
Feedback submitted, thanks!