Steps to configure
The Splunk App for Enterprise Security is designed to support a broad range of environments. After the Splunk App for Enterprise Security has been installed and you are bringing your data into Splunk, you need to configure it for the specifics of your deployment.
Note: If Splunk App for Enterprise Security has not been installed, see "Install Enterprise Security" for information about downloading and installing the app.
In Splunk, select the Enterprise Security app to see the Enterprise Security home page.
Note: To open Configuration from any location in Splunk for Enterprise Security, click the configure icon in the menu bar.
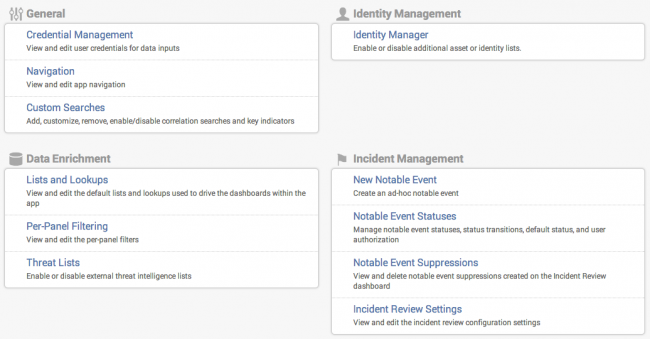
There are several types of information you may want to configure in the Splunk App for Enterprise Security:
- Thresholds for dashboard alerts. Splunk for Enterprise Security includes out-of-the-box thresholds that need to be adjusted for the volume and distribution of the data in your Splunk for Enterprise Security deployment. These thresholds also need to be adjusted over time as you bring new data sources in or as the volume of data coming into Enterprise Security changes.
- Settings for correlation searches and notable events, which can be set with Correlation Searches.
- External information about your environment that needs to be imported into the Splunk App for Enterprise Security, such as: information about the systems and devices (called assets) in your infrastructure; which protocols are allowed on each port; and prohibited ports or services. See "Identity Manager" in this manual and "Assets Manager" in the User Manual for more information.
- Settings that let you determine how you want to use Splunk for Enterprise Security. For example, you can change the choices for Incident Review status, set which dashboards should be reviewed and how often, create different types of users, and set up multiple indexes for different security and retention policies.
Read through this section to understand what needs to be configured in the Splunk App for Enterprise Security.
Configuration overview
When the Splunk App for Enterprise Security is first installed, it will take time for the dashboards to populate. In addition, you must set up supplementary configurations such as the asset list in order to view dashboard content.
After Splunk for Enterprise Security is installed and processing the indexed data, the following items can be configured:
- Review and modify the new user role provided with the Enterprise Security app.
- Define, create, and import the asset list, the identities list, and other external sources data into the Enterprise Security app.
- Set dashboard thresholds
The following two tables show how configurations are used in Splunk for Enterprise Security.
- Table 1: Shows a list of dashboards and the configurations used by each dashboard.
- Table 2: Shows a list of configurations and where they are used in the Splunk App for Enterprise Security
Table 1. List of dashboards and the configurations they require
| Dashboard | Associated configuration | Required? | When to configure |
|---|---|---|---|
| Configure notable events and high-level dashboards | |||
| Security Posture dashboard | Tune dashboard alert thresholds | Recommended | After 2 weeks |
| (Optional) Set up asset latitude and longitude (via asset list) | (Optional) Required by geo map |
At install (if geo map is enabled) | |
| Incident Review dashboard | Create asset list, including priority | Required | At install |
| Create category list | Recommended | At install | |
| Edit correlation search thresholds | Recommended | After 2 weeks | |
| Edit correlation search severity | Advanced | As needed | |
| Disable correlation searches | Advanced | As needed | |
| Edit correlation search governance | Advanced | As needed | |
| Edit notable event status options | Advanced | As needed | |
| Predictive Analytics | |||
| Configure domain dashboards and supporting dashboards | |||
| Domain dashboards and some supporting dashboards | Create asset business units and asset categories (created via asset list and category list) | Required for dashboard filters | At install |
| Malware Center | Tune dashboard alert thresholds | Recommended | After 2 weeks |
| Port and Protocol Tracker | Create Application Protocols list | Required by dashboard | |
| View Auditing dashboard | Create expected views list | Required by dashboard | |
Table 2. List of configurations and where they are used
| Configuration | Where used |
|---|---|
| Thresholds for dashboard alerts | |
| Notable Events by Enterprise Security Domain | Security Posture dashboard |
| Key Malware Statistics | Malware Center dashboard |
| Correlation searches and notable events | |
| Configure status of notable events | Edit Status link on Incident Review and Security Posture dashboards |
| Configure correlation search thresholds | Trigger notable event creation -- not used directly in dashboards. |
| Configure correlation search severity | Notable event Urgency (along with asset priority) |
| Configure correlation search governance | Governance filter on Incident Review dashboard |
| Enable and disable correlation searches | Disable creation of notable events associated with that search |
| Modify correlation searches | Not used directly in dashboards. |
| Change time window for notable event drilldown | Used for event drilldown on all dashboards. |
| Create notable event filters | Not used directly in dashboards. |
| Create a correlation search | Not used directly in dashboards. |
| Lookup lists for external information | |
| Asset list | |
| asset business units | Dashboard filters |
| asset categories | Dashboard filters (used with category list) |
| latitude and longitude | Notable Events by Geography panel in Security Posture dashboard |
| priority | Notable event Urgency (with search severity) |
| Other fields in asset list | Used to augment events, aggregate hosts, and to facilitate event searches |
| Category list | Dashboard filters (used with asset list) |
| Expected Views list | View Auditing dashboard |
| Governance list | Notable event governance |
| Application Protocols blacklist | Port and Protocol Tracker dashboard |
| Prohibited Processes blacklist | Prohibited Processes Detection search |
| Prohibited Services blacklist | Prohibited Service Detection search |
| Identities list | |
| identities business units | Dashboard filters |
| identities categories | Dashboard filters (used with category list) |
| priority | Notable event Urgency (with search severity) |
| Other fields in identities list | Used to augment events, aggregate hosts, and to facilitate event searches |
| Category list | Dashboard filters (used with identity list) |
| Expected Views list | View Auditing dashboard |
Import lists of external information
User-populated lists, most importantly the asset list, provide information about your network and policies that cannot be calculated by Enterprise Security, such as the priority of your hosts or which processes are forbidden. These lists combine the information in your events with external information from CSV files to create additional fields that give more insight into your deployment. Some Enterprise Security dashboards, including the geographic map on the Security Posture dashboard, do not work correctly if this information is not available.
For example, the asset list stores information about the devices on your network, such as priority and location. The Splunk lookup functionality associates the information on the asset list with the source and destination of each event. Then, this association is used to determine the relative urgency and the location of the event.
Use Assets and Identities on the Enterprise Security Home page manage your assets.
Note: Enterprise Security also includes internal lookups that it uses to generate information needed by the correlation searches and other functionality.
Table 3. External lists and where they are used
| List | Description | Where used |
|---|---|---|
| Asset list | Description of the devices on the network | |
| asset business units | Dashboard filters | |
| asset categories | Dashboard filters (used with category list) | |
| latitude and longitude | Notable Events by Geography panel in Security Posture dashboard | |
| priority | Notable event Urgency (with search severity) | |
| Other fields in asset list | Used to augment events, aggregate hosts, and to facilitate event searches | |
| Identity list | Description of the identities using the network | |
| identity business units | Dashboard filters | |
| identity categories | Dashboard filters (used with category list) | |
| priority | Notable event Urgency (with search severity) | |
| Other fields in identity list | Used to augment events, aggregate hosts, | |
| Category list | List of asset categories | Dashboard filters (used with asset list) |
| Expected Views list | List of Enterprise Security dashboards that should be accessed regularly | View Auditing dashboard |
| Application Protocols blacklist | Port/protocol combinations allowed by your organization | Port and Protocol Tracker dashboard |
| Prohibited Processes blacklist | Processes prohibited by your organization | Prohibited Processes Detection search |
| Prohibited Services blacklist | Services prohibited by your organization | Prohibited Service Detection search |
Create user-populated lists
These lists are imported as Splunk lookup tables, which are files in CSV format. The lookup files must be placed on each search head. Splunk automatically loads these lists at search time; you do not need to restart Splunk.
You can supply lookup information from external sources in one of three ways:
- Populate the lookups manually: You can export the data manually and convert it to CSV format for example using Excel. This file can then be copied to the appropriate location on the Search Head using the appropriate tools for your server platform.
- Automatically populate the lookup via a script: It is possible to configure a scripted input to automatically populate a list. Automatic updates can be done using a combination of scripted inputs and custom search commands (written in Python). The implementation details depend on the technology that contains the original information and is therefore beyond the scope of this document. Please contact Splunk Professional Services for additional guidance.
- Paste the content into the Lists and Lookups editor where applicable: Some lookup files have been linked at Configure > Lists and Lookups for updating convenience. New content can be pasted in or typed. This interface does not validate content formatting.
Note: Excel files created on any platform produce CSV files with Windows line endings. The CSV files used as lookups must be created with UNIX-style line endings ("\n"). Splunk will not correctly read lookup files saved using Macintosh ("\r") or Windows line endings ("\r\n"). The dos2unix command can be used to correct this.
Update these lists periodically in order to ensure that Enterprise Security has reasonably up-to-date information. Generally, Splunk recommends that the list be updated at least every quarter.
The following table shows the lookup files and their locations:
| Name | Location under $SPLUNK_HOME/etc/apps/
|
Lookup definition |
|---|---|---|
| Asset list | SA-IdentityManagement/lookups/assets.csv
|
simple_asset_lookup |
| Category list | SA-IdentityManagement/lookups/asset_categories.csv
|
asset_category_lookup |
| Governance list | SA-ThreatIntelligence/lookups/governance.csv
|
governance_lookup |
| Application Protocols whitelist | SA-NetworkProtection/lookups/application_protocols.csv
|
application_protocol_lookup |
| Prohibited Processes blacklist | SA-Threatintelligence/lookups/prohibited_processes.csv
|
prohibited_processes_lookup |
| Prohibited Services blacklist | SA-Threatintelligence/lookups/prohibited_services.csv
|
prohibited_services_lookup |
| Expected Views list | SA-AuditAndDataProtection/lookups/expected_views.csv
|
expected_views_lookup |
| User Account watchlist | SA-AccessProtection/lookups/user_accounts.csv
|
user_account_lookup |
| Identities List | SA-IdentityManagement/lookups/identities.csv
|
simple_identity_lookup |
| Urgencies List | SA-ThreatIntelligence/urgency.csv
|
urgency_lookup |
The table only shows those lookup files that can managed through the Splunk for Enterprise Security UI. There are more lookup files that can be used with the Splunk App for Enterprise Security and its add-ons. This table is a subset of that much larger set of files.
| Install the Splunk App for Enterprise Security | General settings |
This documentation applies to the following versions of Splunk® Enterprise Security: 3.1, 3.1.1, 3.2, 3.2.1, 3.2.2
 Download manual
Download manual
Feedback submitted, thanks!