Create and manage lookups in Splunk Enterprise Security
To configure or edit the lists or lookup files used with the Splunk Enterprise Security, select Configure > Data Enrichment > Lists and Lookups. Use Lists and Lookups to view and edit the default lists and lookups in Enterprise Security.
Click the name of a list to view or edit it. Click Export to export a copy of the file in CSV format.
Internal lookups
Splunk Enterprise Security maintains internal lookups to provide information for dashboards or to create notable events. See Available internal lookups for more details on the lookups included with Splunk Enterprise Security.
These lookups are created in three ways.
- Populated by a static lookup table.
- Populated internally by search commands, called a search-driven lookup.
- Populated with information from the Internet.
The internal lookups populated with information from the Internet are used by some correlation searches to identify hosts that are recognized as malicious or suspicious according to various online sources, such as the SANS Institute. If Splunk Enterprise Security is not connected to the Internet, the lookup files are not updated and the correlation searches that rely on the lookups might not function correctly. Most of the internal lookups populated by the Internet are threat intelligence sources. See Configure the threat intelligence sources included with Splunk Enterprise Security in this manual.
Edit lists and lookups
From the ES menu bar, select Configure > Data Enrichment > Lists and Lookups to view the list of current lookup files. Click a file name to open that lookup file in the lookup editor.
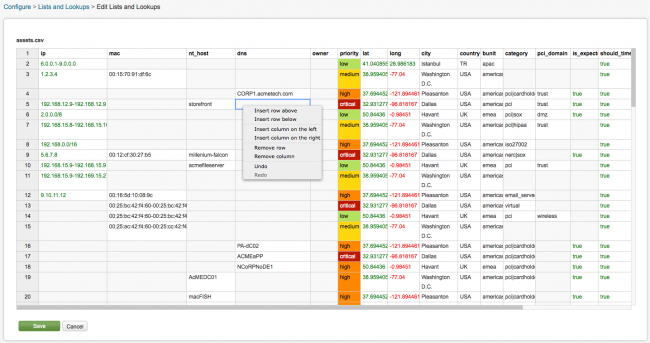
The name of the CSV file is shown in the upper left-hand corner of the panel, assets.csv in this example. The lookup fields are shown at the top of the table, the values for the fields are displayed in the rows below that. Positive numbers are in green, negative numbers are shown in red. The priority values in this file are color-coded. Each CSV file looks slightly different depending on the fields it contains. Lookups do not accept regular expressions.
Only users with appropriate permissions can edit lookups. See Manage permissions in Splunk Enterprise Security in this manual to edit permissions for a user role.
Edit lookup content
- From the ES menu bar, select Configure > Data Enrichment > Lists and Lookups to view the list of current lookup files.
- Click a file name to open that lookup file in the lookup editor.
- Change a value in a cell by selecting the cell and typing the new value.
- Right-click the table to open a context menu that you can use to add columns or rows to the file.
- Click Save to save your changes or Cancel to return to the list of lookups without saving.
Note: You cannot save a lookup file that contains empty header fields.
To review the last time a lookup file was edited and by whom, use a search. For example
index=_internal uri_path="/splunk-es/en-US/app/SplunkEnterpriseSecuritySuite/ess_lookups_edit"
Add new lookup files
An admin might add new CSV files to support new functions and data enrichment in the application. CSV files used as lookups must be created with Unix-style line endings (\n).
Note: CSV files used as lookups must be created with Unix-style line endings ("\n"). Splunk will not correctly read lookup files saved using Macintosh ("\r") or Windows line endings ("\r\n").
- From the Splunk platform system menu, select Settings > Lookups.
- Next to Lookup table files, click Add New.
- Verify that SplunkEnterpriseSecuritySuite is selected as the Destination app.
- Upload a lookup file.
- Type a Destination filename to be displayed in the lookup list.
- Click Save.
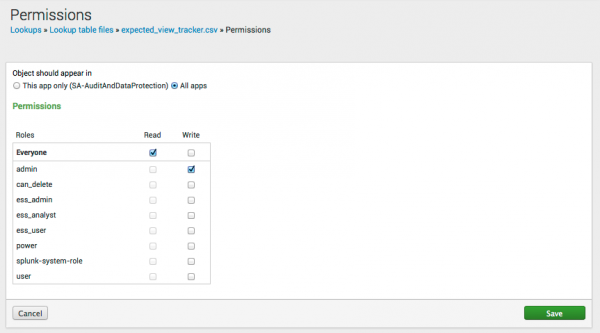
By default, lookups are saved as Private. To share the information with other users, searches, and upgrade events, change the file permissions.
- Click Permissions next to the newly imported CSV file.
- Select the appropriate level and type of permissions for this file. Set access to This app only to limit access to Splunk Enterprise Security or select All apps to allow all apps in this Splunk instance to access the lookup.
- Click Save.
Verify lookup files
Confirm that you added a lookup file successfully by using the inputlookup search command to display the list.
inputlookup append=T application_protocol_lookup
Search-driven lookups
See Create and manage search-driven lookups in Splunk Enterprise Security.
Available internal lookups
The following lookups are available by default in Splunk Enterprise Security. Select Configure > Data Enrichment > Lists and Lookups to view the internal lookups.
Administrative Identities
An account that is known to have administrator or super-user access, such as root or administrator accounts, is considered privileged. Splunk Enterprise Security allows you to identify these privileged accounts so that you can filter to them in relevant dashboards, such as the Access Center dashboard and the Account Management dashboard.
Configure the list of privileged accounts with the Administrative Identities lookup.
- Navigate to Configure > Data Enrichment > Lists and Lookups and select the Administrative Identities lookup.
- The list categorizes privileged default accounts as default|privileged. Select the field and begin typing to make changes.
Application Protocols
The Application Protocols list is a list of port/protocol combinations and their approval status in the organization. This list is used by the Port & Protocol Tracker dashboard. See Port & Protocol Tracker dashboard.
The following fields are available in this file.
| Field | Description |
|---|---|
| dest_port | The destination port number (must be 0-65535) |
| transport | The protocol of the network traffic (icmp, tcp, udp). |
| app | application name |
| status | The approval status of the port (approved, pending, unapproved). By default, the port is considered approved. |
Assets
The Assets lookup contains information about the assets in your environment. This list of assets is matched to incoming events. See Add asset and identity data to Splunk Enterprise Security.
Categories
The category list can contain any set of categories you choose for organizing an asset or an identity. A category is logical classification or grouping used for assets and identities. Common choices for assets include compliance and security standards such as PCI, or functional categories such as server and web_farm. Common choices for identities include titles and roles. For more examples, see Format an asset or identity list as a lookup in Splunk Enterprise Security.
Note: To enrich events with category information in asset and identity correlation, you must maintain the category field in the asset and identity lists rather than the Categories list. See Format an asset or identity list as a lookup in Splunk Enterprise Security.
There are two ways to maintain the Categories list.
Run a saved search to maintain a list of categories
Splunk Enterprise Security includes a saved search that takes categories defined in the asset and identity lists and adds them to the Asset/Identity Categories list. The search is not scheduled by default.
- From the Splunk platform menu bar, select Settings > Searches, reports, alerts.
- Enable the
Identity - Make Categories - Lookup Gensaved search.
Manually maintain a list of categories
Maintain the Categories list manually by adding categories to the lookup directly. By default, you must maintain the list manually.
- Select Configure > Data Enrichment > Lists and Lookups.
- Click the Asset/Identity Categories list.
- Add new categories to the list.
- Save your changes.
Expected Views
The Expected Views list specifies Splunk Enterprise Security views that are monitored on a regular basis. The View Audit dashboard uses this lookup. See View Audit for more about the dashboard.
The following table shows the fields in this file.
| Field | Description |
|---|---|
| app | The application that contains the view (SplunkEnterpriseSecuritySuite) |
| is_expected | Either "true" or "false". If not specified, Splunk Enterprise Security assumes by default that activity is not expected. |
| view | The name of the view. Available in the URL. |
To find the name of a view:
- Navigate to the view in Enterprise Security
- Look at the last segment of the URL to find the view name
For example, the view in the URL below is named incident_review:
![]()
Identities
The Identities lookup contains a list of identities that are matched to incoming events. See Add asset and identity data to Splunk Enterprise Security in this manual.
Interesting Ports
Interesting Ports contains a list of TCP and UDP ports determined to be required, prohibited, or insecure in your deployment. Administrators can set a policy defining the allowed and disallowed ports and modify the lookup to match that policy. To get alerts when those ports are seen in your environment, enable the correlation search that triggers an alert for those ports, such as Prohibited Port Activity Detected.
If you open the lookup file interesting_ports.csv in the lookup editor, the header of the file describes the fields in the file and also described in this table.
| Field | Description | Example |
|---|---|---|
| app | The application or service name | Win32Time |
| dest | The destination host for the network service. Accepts a wildcard. | DARTH*, 10.10.1.100, my_host, etc. Using just a wildcard * will match all hosts.
|
| dest_pci_domain | An optional PCI Domain. Accepts a wildcard. | trust, untrust, etc. |
| dest_port | The destination port number. Accepts a wildcard. | 443, 3389, 5900, etc. |
| transport | The transport protocol. Accepts a wildcard. | tcp or udp |
| is_required | Is the service required to be running? Alert if not present. | true or false |
| is_prohibited | Is the service/traffic/port prohibited from running? Alert if present. | true or false |
| is_secure | Is the service traffic encrypted? | true or false |
| note | A brief description of the service and use-case | Unencrypted telnet services are insecure. |
Interesting Processes
Interesting Processes contains a list of processes. This list is used to determine whether a process is required, prohibited, and/or secure. Use the List and Lookup editor to modify or add to this list. The Interesting Processes lookup is named interesting_processes.csv.
The following table shows the fields in this file.
| Column | Description |
|---|---|
| app | application name |
| dest | destination of process |
| dest_pci_domain | PCI domain, if available |
| is_required | true or false |
| is_prohibited | true or false |
| is_secure | true or false |
| note | Any additional information about this process |
Interesting Services
Interesting Services contains a list of services in your deployment. This list is used to determine whether a service is required, prohibited, and/or secure. Use the List and Lookup editor to modify or add to this list. The Interesting Services is named interesting_services.csv.
The following table shows the fields in this file.
| Column | Description |
|---|---|
| app | application name |
| dest | destination of process |
| dest_pci_domain | PCI domain, if available |
| is_required | true or false |
| is_prohibited | true or false |
| is_secure | true or false |
| note | Any additional information about this process |
Primary Functions
Primary Functions contains a list of primary processes and services, and their function in your deployment. Use this list to designate which services are primary and the port and transport to use. The Primary Functions lookup file is named primary_functions.csv.
The following table shows the fields in this file.
| Column | Description |
|---|---|
| process | name of process |
| service | name of service |
| dest_pci_domain | PCI domain, if available from the asset lookup. See Configure assets in the Splunk App for PCI Compliance Installation and Configuration Manual. |
| transport | tcp or udp |
| port | port number |
| is_primary | true or false |
| function | function of this process (for example, Proxy, Authentication, Database, Domain Name Service (DNS), Web, Mail) |
Prohibited Traffic
Prohibited Traffic lists processes that will generate an alert if they are detected. This list is used by the System Center dashboard and is useful for detecting software that is prohibited by the security policy, such as IRC or data destruction tools, or for software that is known to be malicious, such as malware that was recently implicated in an outbreak.
The Prohibited Traffic file is named prohibited_traffic.csv.
The following table shows the fields in this file.
| Field | Description |
|---|---|
| app | The name of the process (such as echo, chargen, etc.) |
| is_prohibited | Either "true" or "false" |
| note | A text description of why the process is rejected |
Urgency Levels
Urgency Levels contains the combinations of priority and severity that dictate the urgency of notable events. See How urgency is assigned to notable events in Splunk Enterprise Security in Use Splunk Enterprise Security.
| Export content from Splunk Enterprise Security as an app | Create risk and edit risk objects in Splunk Enterprise Security |
This documentation applies to the following versions of Splunk® Enterprise Security: 4.7.0, 4.7.1, 4.7.2, 4.7.3, 4.7.4, 4.7.5, 4.7.6
 Download manual
Download manual
Feedback submitted, thanks!