Configure Windows event logging to ensure the proper events are logged
Configure Windows event logging to make sure that the events required for behavioral analytics service detections are logged.
Behavioral analytics service detections require 4688, 4103, and 4104 events in order to generate anomalies. See Supported data sources in behavioral analytics service for a complete list of supported Windows events.
Install the Splunk Add-on for Microsoft Windows on your heavy forwarder
Make sure you have installed the latest version of the Splunk Add-on for Microsoft Windows on the heavy forwarder you are using to send data to behavioral analytics service. You can obtain the Splunk Add-on for Microsoft Windows on Splunkbase.
The Splunk Add-on for Microsoft Windows changes the sourcetype from WinEventLog:Security to WinEventLog so that behavioral analytics service can properly recognize and parse the events.
Enable command line process logging for 4688 events
Microsoft Windows 4688 events contain audit information for command line processes. To enable 4688 events to be logged, perform the following tasks:
- Enable Audit Process Creation.
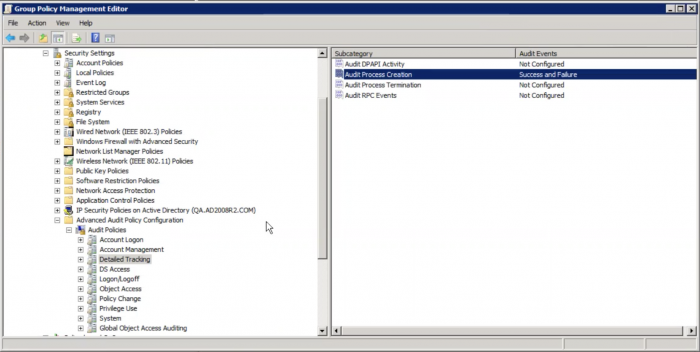
- Go to the policy editor on your local Windows machine. The policy is located at Computer Configuration > Policies > Windows Settings > Security Settings > Advanced Audit Configuration > Detailed Tracking.
- Double-click Audit Process Creation.
- Select both the Success and Failure checkboxes in the Audit Process Creation Properties window.
- Click OK. You can verify your setting if both Success and Failure appear in the Audit Events column, as shown in the following image:
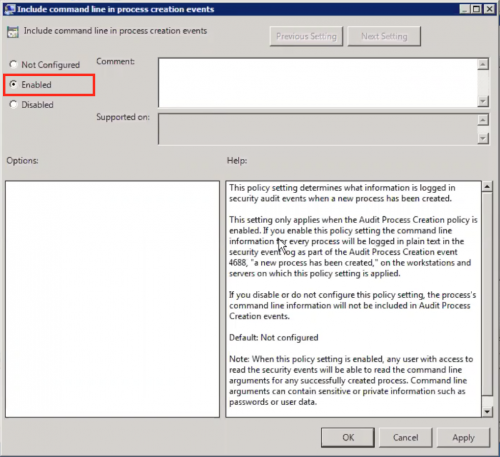
- Enable Include command line in process creation events.
If you are using automation software, such as Ansible, for remote configurations, use the following script to enable command line process logging:
- name: Enable Command Line Audit for Windows Sec. Events 4688
ignore_errors: yes
when: win_4688_cmd_line == "1"
win_regedit:
key: "HKLM:\\Software\\Microsoft\\Windows\\CurrentVersion\\Policies\\System\\Audit"
value: ProcessCreationIncludeCmdLine_Enabled
datatype: dword
data: 1
- name: Enable New Process Creation. Events 4688
ignore_errors: yes
when: win_4688_cmd_line == "1"
win_audit_policy_system:
subcategory: Process Creation
audit_type: success, failure
See "Command line process auditing" in the Microsoft documentation for more information.
Enable PowerShell logging for 4103 and 4104 events
PowerShell provides access to Windows API calls that attackers can exploit to gain elevated access to the system, avoiding antivirus and other security controls in the process. PowerShell is also internally utilized by popular hacking tools.
Perform the following tasks to properly enable PowerShell logging:
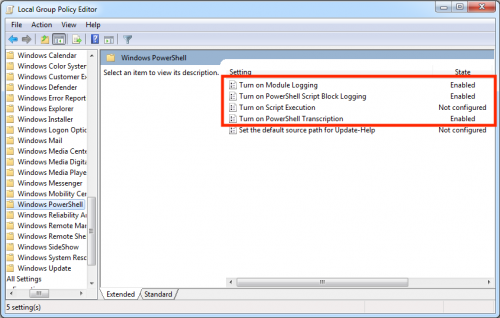
- On your local Windows system, navigate to Administrative Templates > Windows Components > Windows PowerShell.
- Double-click Turn on Script Execution.
- Click the Enabled checkbox.
- Select an execution policy from the drop-down list in the Execution Policy field. In the following image, the Allow all scripts policy is selected.
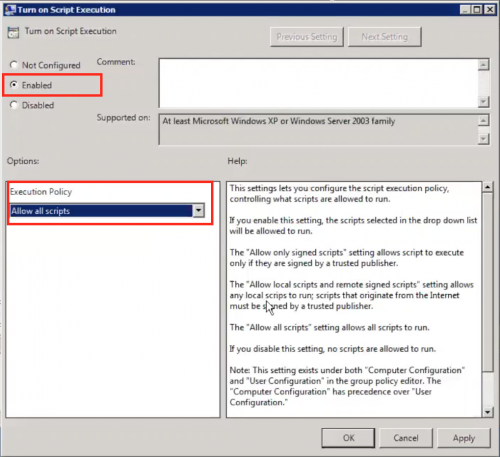
- Click Apply.
- Click OK to dismiss the window.
- Repeat the process and also enable Turn on Module Logging, Turn on PowerShell Script Block Logging, and Turn on PowerShell Transcription. The following image shows the additional options:
If you are using automation software, such as Ansible, for remote configurations, use the following script to enable PowerShell logging:
- name: Enable Windows Scriptblock Logging
ignore_errors: yes
win_regedit:
key: "HKLM:\\Software\\Policies\\Microsoft\\Windows\\PowerShell\\ScriptBlockLogging"
value: EnableScriptBlockLogging
datatype: dword
data: 1
- name: Enable Windows Scriptblock Logging
ignore_errors: yes
win_regedit:
key: "HKLM:\\Software\\Policies\\Microsoft\\Windows\\PowerShell\\ScriptBlockLogging"
value: EnableScriptBlockInvocationLogging
datatype: dword
data: 1
- name: restart machine
win_reboot:
See "About Logging Windows" in the Microsoft documentation for more information.
| Select which data sources to use with behavioral analytics service | Leverage operational logging for self-service supportability |
This documentation applies to the following versions of Splunk® Enterprise Security: 7.0.1, 7.0.2
 Download manual
Download manual
Feedback submitted, thanks!