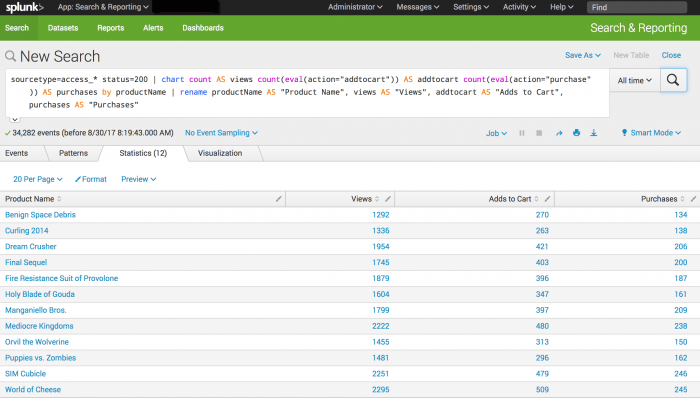
Create a basic chart
In this example you compare the counts of user actions by calculating information about the actions customers have taken on the online store website.
- The number of times each product is viewed
- The number of times each product is added to the cart
- The number of times each product is purchased
Prerequisite
This example requires the productName field from the Enabling field lookups section. You must complete all of those steps before continuing with this section.
Steps
- Start a new search.
- Set the time range to All time.
- Run the following search.
sourcetype=access_* status=200 | chart count AS views count(eval(action="addtocart")) AS addtocart count(eval(action="purchase")) AS purchases by productName | rename productName AS "Product Name", views AS "Views", addtocart AS "Adds to Cart", purchases AS "Purchases"
- This search uses the
chartcommand to count the number of events that areaction=purchaseandaction=addtocart. The search then uses therenamecommand to rename the fields that appear in the results.
- The
chartcommand is a transforming command. The results of the search appear on the Statistics tab.
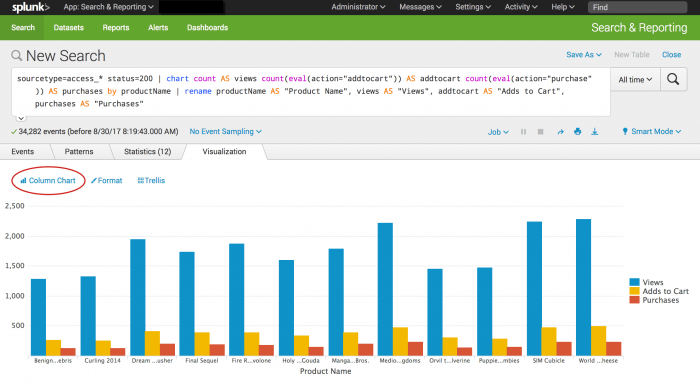
- Click the Visualization tab. The search results appear in a Pie chart.
- Change the display to a Column chart.
Next step
Create an overlay chart and explore visualization options
See also
chart command in the Search Reference
rename command in the Search Reference
Transforming commands in the Search Manual
| Save and share your reports | Create an overlay chart and explore visualization options |
This documentation applies to the following versions of Splunk® Enterprise: 7.0.0, 7.0.1, 7.0.2, 7.0.3, 7.0.4, 7.0.5, 7.0.6, 7.0.7, 7.0.8, 7.0.9, 7.0.10, 7.0.11, 7.0.13
 Download manual
Download manual
Feedback submitted, thanks!