Export data using Splunk Web
You can export the event data from a search, report, or pivot job to various formats. You can then archive the file, or use the file with a third-party charting application.
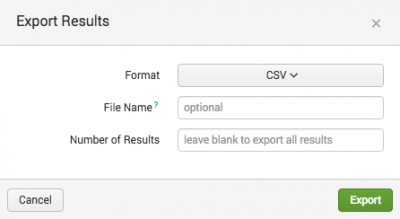
- After you run a search, report, or pivot, click the Export button. The Export button is one of the Search action buttons.
- Click Format and select the format that you want the search results to be exported in.
- The supported formats depend on the type of job artifact that you are working with.
Format Ad hoc searches Saved searches Notes CSV X X JSON X X PDF X If the search is a saved search, such as a Report, you can export using the PDF format. Raw Events X X If the search generates calculated data that appears on the Statistics tab, you cannot export using the Raw Events format. XML X X - Optional. In the File Name field, you can type a name for the export file where the event data will be stored.
- If you do not specify a file name, a file is created using the search job ID as the file name. The search job ID is the UNIX time when the search was run. For example
1463687468_7.csv. - Optional. In the Number of Results field, you can specify the number of results that you want to export. If you do not specify a number, all of the events are exported.
- For example, if you specify 500 in the Number of Results field, only the first 500 results returned from your search are exported.
- Click Export to save the job events in the export file.
- The file is saved in the default download directory for your browser or operating system. For example, for most Windows and Mac OS X users the export file appears in the default Downloads directory. On Linux, check the XDG configuration file for the download directory.
If the button is not visible, the button has been hidden by your system administrator to prevent data export.
Sometimes your search must be run again before the results can be exported. See When exporting triggers your search to run again.
When exporting triggers your search to run again
If your search returns a large number of results, it is possible that not all of the results will be stored with the search job artifact.
When you export search results, the export process is based on the search job artifact, not the results in the Search app. If the artifact does not contain the full set of results, a message appears at the bottom of the Export Results dialog box to tell you that the search will be rerun by the Splunk software before the results are exported.
The search is rerun when the search head believes that it cannot retrieve all of the events from the job artifact. The search head determines when to rerun the search based on the following logic:
- If the search is not a report, and one of the following is true.
- The search is not done
- The search is using a remote timeline
- The search head believes that the search has not retained all of events
Extend the session timeout when exporting large amounts of data
When you export large amounts of data using the Export button, the session might timeout before the export is complete. You can extend the session timeout limit.
- Click Settings > Server Settings > General Settings.
- In the Splunk Web section, increase the number in the Session timeout field.
- Click Save.
Increase the timeout setting to allow more time for the connection between your browser and Splunk Web.
Forward data to third-party systems
You can forward the data that you export to third-party systems.
- For an brief overview, see Forward data to third party systems in this manual.
- For more details, see Forward data to third party systems in Forwarding Data.
Use reports to send results to stakeholders
You can schedule reports to run on a regular interval and send the results to project stakeholders by email. The emails can present the report results in tables in the email, and as CSV or PDF attachments. The emails can also include links to the report results in Splunk Enterprise. See Schedule Reports in the Reporting Manual.
| Export search results | Export data using the CLI |
This documentation applies to the following versions of Splunk® Enterprise: 7.0.0, 7.0.1, 7.0.2, 7.0.3, 7.0.4, 7.0.5, 7.0.6, 7.0.7, 7.0.8, 7.0.9, 7.0.10, 7.0.11, 7.0.13
 Download manual
Download manual
Feedback submitted, thanks!