Setting up a scripted input
This section describes how to set up a scripted input for an app. To illustrate the setup, it uses an example script that polls a database and writes the results to a file. A more detailed version of this example is in Example script that polls a database. That topic provides details on the example, including code examples in Python and Java.
You can write any number and types of scripts in various scripting languages that perform various functions. This example shows the framework for a commonly found script. Adapt this framework according to your needs.
Script to poll a database
This example script does the following.
- Runs at a regular interval.
- Queries a database.
- Writes the output to a file in a format optimized for indexing.
- Splunk software indexes the file containing the results of the queries.
Directory structure
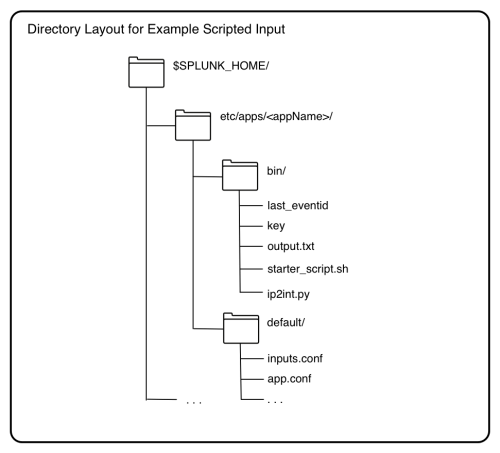
Place scripts in the /bin directory of your app.
$SPLUNK_HOME/etc/apps/<appName>/bin/
Here is the directory structure of the example script for this example. The directory structure for your app might differ.
Script files
. . ./etc/apps/<appName>/bin/my_db_poll.py
This is the script that retrieves information from the database. This script does the following:
- Queries the database and writes the query result to file.
- Defines the format of output data.
- Accesses a database using credentials stored in key.
- Reads last_eventid to determine the next event to read from the database.
- Queries the database at the next event and writes the output to a file.
. . ./etc/apps/<appName>/bin/starter_script.sh
Wrapper script that calls the my_db_poll.py script. In this example, it calls my_db_poll.py with the arguments needed to query the database.
In .../etc/apps/<appName>/default/inputs.conf, create a stanza that references this wrapper script. In this example, the stanza specifies how often to call the starter script to poll the database.
. . ./etc/apps/<appName>/bin/ip2int.py
A helper script to convert IP addresses from integer format to dotted format, and back. This is a type of helper script that formats data better for indexing. You often have helper scripts that aid the main script.
. . ./etc/apps/<appName>/bin/key
Text file containing username and password encoded in base64 using the python function base64.b64encode(). The Splunk Enterprise user has read and write access to this file.
Security for passwords is an issue when running scripts.
. . ./etc/apps/<appName>/bin/last_eventid
File containing a number for the last event received from the database. my_db_poll.py writes the last_eventid after querying the database. The Splunk user has read and write access to this file.
'. . ./etc/apps/<appName>/bin/output.txt'
A single event from the script, for reference. my_db_poll.py writes the actual output from querying the database to another directory.
. . ./etc/apps/<appName>/default/inputs.conf
Configure scripted data input in $SPLUNK_HOME/etc/<appName>/default/inputs.conf. Use the local directory for the app to overwrite behavior defined in the default directory. Here is an example:
[script://$SPLUNK_HOME/etc/apps/<appName>/bin/starter_script.sh] disabled = true # change to false to start the input, requires restart host = # enter hostname here index = main interval = 30 #frequency to run the script, in seconds source = my_db sourcetype = my_db_data
$SPLUNK_HOME/etc/system/local/props.conf
Configure properties for the script in the Splunk Enterprise system props.conf.
[my_db_data] TIME_PREFIX=^[^\|]+\| TIME_FORMAT=%Q MAX_TIMESTAMP_LOOKAHEAD=10 #look ahead 10 characters SHOULD_LINEMERGE=false
$SPLUNK_HOME/etc/system/local/transforms.conf
Define field transforms in transforms.conf.
[my_db_extractions] DELIMS = "|" FIELDS ="EventID","AlertTime","UserName",. . ."
| Modular inputs examples | Writing reliable scripts |
This documentation applies to the following versions of Splunk® Enterprise: 7.0.0, 7.0.1, 7.0.2, 7.0.3, 7.0.4, 7.0.5, 7.0.6, 7.0.7, 7.0.8, 7.0.9, 7.0.10, 7.0.11, 7.0.13, 7.1.0, 7.1.1, 7.1.2, 7.1.3, 7.1.4, 7.1.5, 7.1.6, 7.1.7, 7.1.8, 7.1.9, 7.1.10, 7.2.0, 7.2.1, 7.2.2, 7.2.3, 7.2.4, 7.2.5, 7.2.6, 7.2.7, 7.2.8, 7.2.9, 7.2.10, 7.3.0, 7.3.1, 7.3.2, 7.3.3, 7.3.4, 7.3.5, 7.3.6, 7.3.7, 7.3.8, 7.3.9, 8.0.0, 8.0.1, 8.0.2, 8.0.3, 8.0.4, 8.0.5, 8.0.6, 8.0.7, 8.0.8, 8.0.9, 8.0.10, 8.1.0, 8.1.1, 8.1.2, 8.1.3, 8.1.4, 8.1.5, 8.1.6, 8.1.7, 8.1.8, 8.1.9, 8.1.10, 8.1.11, 8.1.12, 8.1.13, 8.1.14, 8.2.0, 8.2.1, 8.2.2, 8.2.3, 8.2.4, 8.2.5, 8.2.6, 8.2.7, 8.2.8, 8.2.9, 8.2.10, 8.2.11, 8.2.12, 9.0.0, 9.0.1, 9.0.2, 9.0.3, 9.0.4, 9.0.5, 9.0.6, 9.0.7, 9.0.8, 9.0.9, 9.0.10, 9.1.0, 9.1.1, 9.1.2, 9.1.3, 9.1.4, 9.1.5, 9.1.6, 9.1.7, 9.1.8, 9.1.9, 9.2.0, 9.2.1, 9.2.2, 9.2.3, 9.2.4, 9.2.5, 9.2.6, 9.3.0, 9.3.1, 9.3.2, 9.3.3, 9.3.4, 9.4.0, 9.4.1, 9.4.2
 Download manual
Download manual
Feedback submitted, thanks!