Search modes
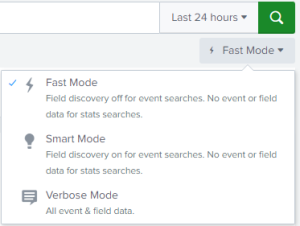
You can use the Search Mode selector to provide a search experience that fits your needs. The search mode selector is on the right side of and slightly below the Search bar.
You can choose from the following modes in the search mode selector:
- Fast
- Smart
- Verbose
The default search mode is Smart mode.
Depending on the mode you set when you run a search, you can see all the data available for your search, but at the expense of longer search times, or you can speed up and streamline your search in certain ways. The Fast and Verbose modes represent the two ends of that search mode spectrum.
Smart mode is the best choice for most searches and is the middle ground between the Fast and Verbose modes. The Smart mode switches between the Fast and Verbose modes depending on the type of search that you are running.
When you run a report, Splunk platform uses the same search mode that was in effect when you initially saved the search. When you schedule a report, Splunk platform uses the Smart search mode, by default, and doesn't allow you to specify a different search mode.
Using the Fast mode
The Fast mode prioritizes the performance of the search and only returns essential event data, such as default fields and fields that were extracted at index time. Because field discovery for events is turned off, the Fast mode doesn't perform any search-time field extraction. However, the Fast mode does return search-time fields that you explicitly add to the search.
Since the Fast mode is optimized for speed, there might be disparities in values of fields compared to the Smart or Verbose modes. But, the number of results returned in searches using the Fast mode are consistent with the number of results returned by the other modes.
The Fast mode does the following:
- Extracts default fields such as
host,source, andsourcetype. The fast mode only returns information on indexed and default fields, and any search-time extracted fields that you explicitly include in your search. If you're searching on specific indexed fields, those fields are also extracted. - For searches with transforming commands, depicts search results by displaying a visualization, such as a chart.
- For searches that don't include transforming commands, displays event lists and event timelines.
Most of the time, your ad hoc searches should use the Smart mode, but there are certain specific cases where it makes sense to use the Fast mode instead. For example, use the Fast mode in the following situations:
- When you need to do basic field discovery and you don't care about the accuracy of your field extractions. For example, perhaps you just want to see what is in a particular source type, source, or host field.
- When you don't know what's in your index. For example, perhaps you want to know what indexed fields are in your index.
- When you want to know how many events are in your index and how frequently they occur in your data. For example, perhaps you want to find out the volume of events and approximately how many events you're getting during a particular slice of time, such as 500,000 events in a day.
- When you want to run reporting searches that include transforming commands that return results in charts or visualizations.
- When you don't care whether your events have extracted fields that aren't mentioned in your search.
For more information about what the Splunk platform does when field discovery is turned on or off, see When extracts fields in the Knowledge Manager Manual.
Using the Smart mode
All reports run in Smart mode, the default search mode, after they are first created. The Smart mode returns the best results for whatever search or report you run. If you search on events, field discovery for event searches is turned on and you get all the event information you need. If you run a transforming search, the Splunk platform favors speed over thoroughness and takes you quickly to the report result table or visualization.
When you run a Smart mode search that does not include transforming commands, the search behaves as if it were in Verbose mode.
- All possible fields are discovered.
- The full event list and event timeline are generated. No event table or visualization will appear because you need transforming commands to make those happen.
When you run a Smart mode search that includes transforming commands, the search behaves as if it were in Fast mode.
- Field discovery is disabled.
- Your search does not waste time generating the event list and event timeline, and jumps you straight to the report result table or visualization.
For more information about transforming commands and transforming searches, see About reporting commands in the Search Manual.
Using the Verbose mode
The Verbose mode returns all of the field and event data it possibly can, even if it means the search takes longer to complete, and even if the search includes reporting commands.
- Your search discovers all of the fields it can. This includes default fields, automatic search-time field extractions, and all user-defined index-time and search-time field extractions. Discovered fields are displayed in the left-hand fields sidebar in the Events results tab.
- Your search returns an event list view of results and generates the search timeline. It also generates report tables and visualizations if your search includes reporting commands.
You may want to use the Verbose mode if you are putting together a transforming search, but are not exactly sure which fields you need to report on, or if you need to verify that you are summarizing the correct events.
Reports cannot benefit from report acceleration when you run them in Verbose mode. If you turn on report acceleration for a report and it has been running faster as a result, be aware that if you switch the mode of the search to Verbose it will run at a slower, non-accelerated pace.
Report acceleration is designed to be used with slow-completing searches that have over 100,000 events and which utilize transforming commands. For more information see Accelerate reports, in the Reporting Manual.
Comparing search modes
The following table compares the key differences between the different search modes.
| Search mode | Optimized for | Field extraction behavior | Displays |
|---|---|---|---|
| Fast |
|
|
|
| Smart |
|
Field Discovery is:
|
|
| Verbose |
|
|
|
See also
| Search actions | Search history |
This documentation applies to the following versions of Splunk Cloud Platform™: 9.3.2411 (latest FedRAMP release), 8.2.2203, 9.0.2205, 9.0.2208, 8.2.2201, 8.2.2202, 9.0.2209, 9.0.2303, 9.0.2305, 9.1.2308, 9.1.2312, 9.2.2403, 9.2.2406, 9.3.2408
 Download manual
Download manual
Feedback submitted, thanks!