Investigate threats from Splunk UBA using Splunk Enterprise Security
Threats sent from Splunk UBA to Splunk Enterprise Security (ES) appear as notable events on the Incident Review and Security Posture dashboards. You can see the count of notable events created from threats on the Security Posture dashboard as a Key Security Indicator (KSI).
On Incident Review, you can expand the event details to see the description, threat category, correlation search referencing Splunk UBA, and more details. Use the workflow actions on the event to view contributing anomalies and open the Threat Details page in Splunk UBA.
Integrating Splunk UBA to send threats to Splunk ES as notable events and synchronizing the status of the threats and notable events on both systems is enabled by default.
To send events from Splunk UBA to Splunk Enterprise without using Splunk ES, add the uba.splunkes.integration.enabled property to the /etc/caspida/local/conf/uba-site.properties file and set the property to false. See Send Splunk UBA data to Splunk Enterprise without Splunk Enterprise Security in Administer Splunk User Behavior Analytics.
Use Splunk ES to close or reopen notable events in order to have the corresponding threats also be closed or reopened in Splunk UBA. Do not close or reopening threats in Splunk UBA.
Configure an output connector to send threats from Splunk UBA to Splunk ES
Follow the instructions in Send Splunk UBA anomalies and threats to Splunk ES to configure an output connector to send threats and anomalies from Splunk UBA to Splunk ES.
Once the output connector is configured, Splunk UBA attempts to send threats to Splunk ES every five minutes with no limits on the number of retries. Any issues with the connection mean that new threats will not be sent to Splunk ES until the connection issues are resolved. Any connection issues between the output connector and Splunk ES also affect other output connectors that may be configured, such as email and ServiceNow. If the connection issues persist for more than one hour, alerts are generated in the health monitor in Splunk UBA. See Monitor the health of your Splunk UBA deployment.
Perform the following tasks if you want to change the retry interval:
- On the Splunk UBA master node, login as the caspida user.
- Edit the
etc/caspida/local/conf/uba-site.propertiesfile and modify theuba.splunkes.retry.delay.minutesproperty. For example, to set the retry interval to 3 mintues:uba.splunkes.retry.delay.minutes = 3
- In distributed deployments, synchronize the cluster:
/opt/caspida/bin/Caspida sync-cluster /etc/caspida/local/conf
Work with Splunk UBA threats as notable events in Splunk Enterprise Security
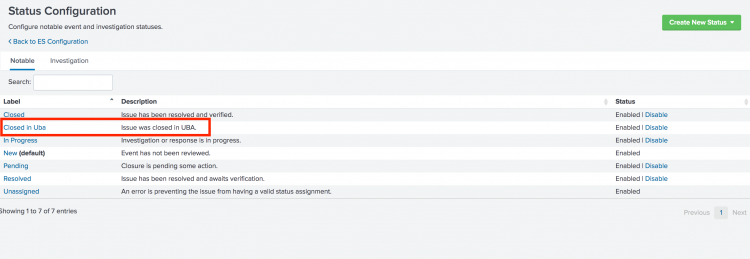
When Splunk UBA and Splunk ES are integrated using an output connector, Splunk UBA creates a new custom status on Splunk ES called Closed in Uba. The status of threats in Splunk UBA and their corresponding notable events in Splunk ES are synchronized.
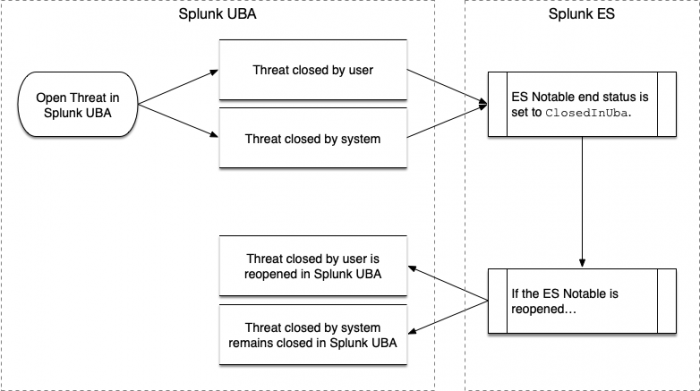
What happens when a threat is closed in Splunk UBA
Threats in Splunk UBA can be closed by the user, or closed by the system:
- Threats in Splunk UBA are considered closed by the user if Not a Threat is clicked in Splunk UBA.
- In all other cases, the threat in Splunk UBA is considered to be closed by the system.
When a threat is closed in Splunk UBA, Splunk UBA checks the status of the corresponding notable event in Splunk ES. If the notable event is not already closed in Splunk ES, Splunk UBA closes the notable event by setting the end status to Closed in Uba.
If the notable event is reopened in Splunk ES, a threat closed by the user in Splunk UBA is reopened. A threat closed by the system remains closed in Splunk UBA. The threat can still be viewed, but no action can be taken on the threat.
What happens when a threat is reopened in Splunk UBA
A threat in Splunk UBA can be reopened in the following cases:
- Threat computation causes a threat to be reopened
- An anomaly action rule affects anomalies that cause a threat to be reopened
- A threat rule is modified, causing a threat to be reopened
When a threat is reopened, Splunk UBA checks to see if the notable event in Splunk ES has an end status of ClosedInUba and if yes, the notable event is also reopened.
No action is taken if the notable event is already open in Splunk ES, or if it has an end status other than ClosedInUba.
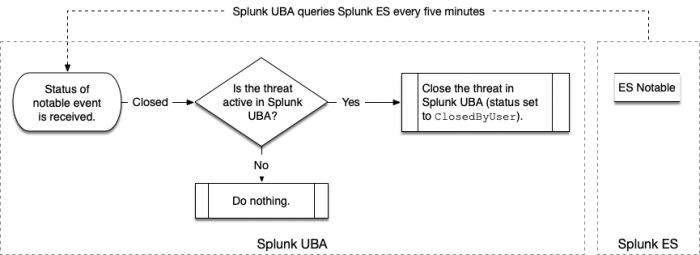
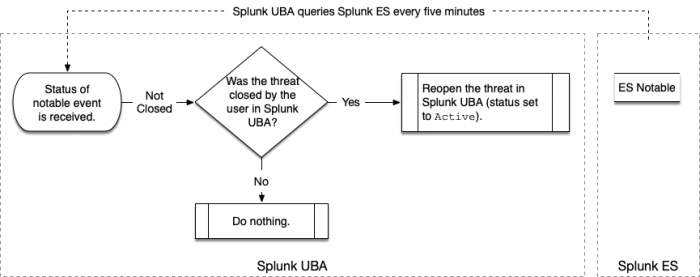
Splunk UBA queries for the status of notable events in Splunk ES
Splunk UBA queries Splunk ES in five-minute intervals to synchronize the status of threats in Splunk UBA and notable events in Splunk ES.
When the query detects that a notable event is closed, Splunk UBA checks to see if the corresponding threat is also closed. If not, the threat is closed with a status of ClosedbyUser.
When the query detects that a notable event is not closed, Splunk UBA checks to see if the corresponding threat has a status of ClosedbyUser. If so, the threat is reopened with a status of Active.
What happens if the output connector is unable to send threats to Splunk ES
If the output connector is unable to send threats to Splunk ES, due to a network issue or Splunk ES being temporarily unavailable, the output connector will make another attempt every five minutes. After one hour, if the connection is not resolved, the output connector will raise an error in the health monitor. See OCS-11.
| Send audit events to Splunk ES |
This documentation applies to the following versions of Splunk® Add-on for Splunk UBA: 3.0.0
 Download manual
Download manual
Feedback submitted, thanks!