iplocation
Description
Extracts location information from IP addresses by using 3rd-party databases. This command supports IPv4 and IPv6.
The IP address that you specify in the ip-address-fieldname argument, is looked up in the database. Fields from that database that contain location information are added to each event. The setting used for the allfields argument determines which fields are added to the events.
Because all the information might not be available for each IP address, an event can have empty field values.
For IP addresses which do not have a location, such as internal addresses, no fields are added.
Syntax
iplocation [prefix=<string>] [allfields=<bool>] [lang=<string>] <ip-address-fieldname>
Required arguments
- ip-address-fieldname
- Syntax: <field>
- Description: Specify an IP address field, such as
clientip.
Optional arguments
- allfields
- Syntax: allfields=<bool>
- Description: Specifies whether to add all of the fields from the database to the events. If set to
true, adds the fields City, Continent, Country, lat (latitude), lon (longitude), MetroCode, Region, and Timezone. - Default: false. Only the City, Country, lat, lon, and Region fields are added to the events.
- lang
- Syntax: lang=<string>
- Description: Render the resulting strings in different languages. For example, use "lang=es" for Spanish. The set of languages depends on the geoip database that is used. To specify more than one language, separate them with a comma. This also indicates the priority in descending order. Specify "lang=code" to return the fields as two letter ISO abbreviations.
- prefix
- Syntax: prefix=<string>
- Description: Specify a string to prefix the field name. With this argument you can add a prefix to the added field names to avoid name collisions with existing fields. For example, if you specify
prefix=iploc_the field names that are added to the events becomeiploc_City,iploc_County,iploc_lat, and so forth. - Default: NULL/empty string
Usage
The iplocation command is a distributable streaming command. See Command types.
The Splunk software ships with a copy of the GeoLite2-City.mmdb database file. This file is located in the $SPLUNK_HOME/share/ directory.
Updating the MMDB file
You can replace the version of the .mmdb file that ships with the Splunk software with a copy of the paid version of the file or with a monthly update of the free version of the file.
- From http://dev.maxmind.com/geoip/geoip2/geolite2/, download the binary gzipped version of the GeoLite2 City database file.
- Copy the file to the search head on your Splunk Enterprise instance.
- Expand the GZ file.
- Stop any real-time searches that are running.
- Copy the GeoLite2-City.mmdb file to the
$SPLUNK_HOME/share/directory to overwrite the file there. - Restart the real-time searches.
Impact of upgrading Splunk software
When you upgrade your Splunk platform, the GeoLite2-City.mmdb file in the share directory is replaced by the version of the file that ships with the Splunk software. One option is to store the MMDB file in a different path.
Storing the MMDB file in a different path
If you prefer to update the GeoLite2-City.mmdb file yourself, for example if you use a paid version of the file, you can store the MMDB file in a different path. The path that is used by the Splunk software to access the file must be updated.
Prerequisites
- Only users with file system access, such as system administrators, can specify a different path to the MMDB file in the
limits.conffile. - Review the steps in How to edit a configuration file in the Admin Manual.
- You can have configuration files with the same name in your default, local, and app directories. Read Where you can place (or find) your modified configuration files in the Admin Manual.
Never change or copy the configuration files in the default directory. The files in the default directory must remain intact and in their original location. Make the changes in the local directory.
If you use Splunk Cloud Platform, updates to the MMDB file are provided ONLY with Splunk version upgrades. If you wish to discuss or request this, file a Support ticket.
Steps
- Open the local
limits.conffile for the Search app. For example,$SPLUNK_HOME/etc/system/local. - Add the
[iplocation]stanza. - Add the
db_pathsetting and specify the absolute path to theGeoLite2-City.mmdbfile. Thedb_pathsetting does not support standard Splunk environment variables such as$SPLUNK_HOME.
For example:db_path = /Applications/Splunk/mmdb/GeoLite2-City.mmdbspecifies a new directory calledmmdb. - Ensure a copy of the MMDB file is stored in the
../Applications/Splunk/mmdb/directory. - Because you are editing the path to the MMDB file, you should restart the Splunk server.
Storing the MMDB file with a different name
Alternatively, you can add the updated MMDB to the share directory using a different name and then specify that name in the db_path setting. For example: db_path = /Applications/Splunk/share/GeoLite2-City_paid.mmdb.
The MMDB file and distributed deployments
The iplocation command is a distributable streaming command, which means that it can be processed on the indexers. The share directory is not part of the knowledge bundle. If you update the MMDB file in the share directory, the updated file is not automatically sent to the indexers in a distributed deployment. To add the MMDB file to the indexers, use the tools that you typically use to push files to the indexers.
Examples
1. Add location information to web access events
| This example uses the sample data from the Search Tutorial but should work with any format of Apache web access log. To try this example on your own Splunk instance, you must download the sample data and follow the instructions to get the tutorial data into Splunk. Use the time range All time when you run the search. |
Add location information to web access events. By default, the iplocation command adds the City, Country, lat, lon, and Region fields to the results.
sourcetype=access_* | iplocation clientip
2. Search for client errors and return the first 20 results
| This example uses the sample data from the Search Tutorial but should work with any format of Apache web access log. To try this example on your own Splunk instance, you must download the sample data and follow the instructions to get the tutorial data into Splunk. Use the time range All time when you run the search. |
Search for client errors in web access events, returning only the first 20 results. Add location information and return a table with the IP address, City, and Country for each client error.
sourcetype=access_* status>=400 | head 20 | iplocation clientip | table clientip, status, City, Country
The results appear on the Statistics tab and look something like this:
| clientip | status | City | Country |
|---|---|---|---|
| 182.236.164.11 | 408 | Zhengzhou | China |
| 198.35.1.75 | 500 | Princeton | United States |
| 198.35.1.75 | 404 | Princeton | United States |
| 198.35.1.75 | 406 | Princeton | United States |
| 198.35.1.75 | 500 | Princeton | United States |
| 221.204.246.72 | 503 | Taiyuan | China |
| 1.192.86.205 | 503 | Amesbury | United States |
| 91.205.189.15 | 406 | ||
| 216.221.226.11 | 505 | Redwood City | United States |
| 216.221.226.11 | 404 | Redwood City | United States |
| 195.2.240.99 | 400 | Russia |
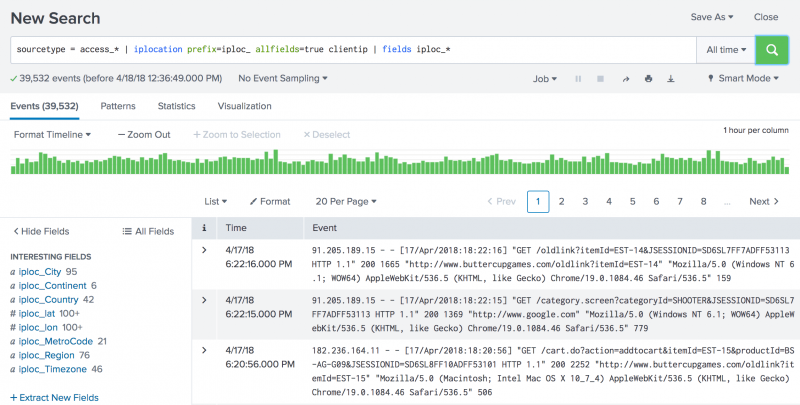
3. Add a prefix to the fields added by the iplocation command
Prefix the fields added by the iplocation command with iploc_. Add all of the fields in the GeoLite2-City.mmdb database file to the results.
sourcetype = access_* | iplocation prefix=iploc_ allfields=true clientip | fields iploc_*
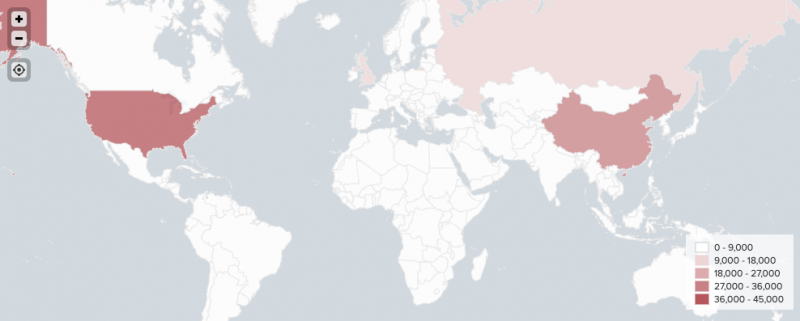
4. Generate a choropleth map using IP addresses
Generate a choropleth map of your data like the one below using the iplocation command. See Use IP addresses to generate a choropleth map in Dashboards and Visualizations.
| inputlookup | join |
This documentation applies to the following versions of Splunk® Enterprise: 7.1.0, 7.1.1, 7.1.2, 7.1.3, 7.1.4, 7.1.5, 7.1.6, 7.1.7, 7.1.8, 7.1.9, 7.1.10, 7.2.0, 7.2.1, 7.2.2, 7.2.3, 7.2.4, 7.2.5, 7.2.6, 7.2.7, 7.2.8, 7.2.9, 7.2.10, 7.3.0, 7.3.1, 7.3.2, 7.3.3, 7.3.4, 7.3.5, 7.3.6, 7.3.7, 7.3.8, 7.3.9, 8.0.0, 8.0.1, 8.0.2, 8.0.3, 8.0.4, 8.0.5, 8.0.6, 8.0.7, 8.0.8, 8.0.9, 8.0.10
 Download manual
Download manual
Feedback submitted, thanks!