Search history
There are several ways to view your search history for searches that you have previously run.
The search history is available only for the app you're currently using. For example, if you run a search in another Splunk app, the search history for that app will not be visible in the search history in the Search app.
Search history in the Search Summary view
Your full search history appears at the bottom of the Search Summary view.
Use the Search History panel to view and interact with the searches that you have previously run.
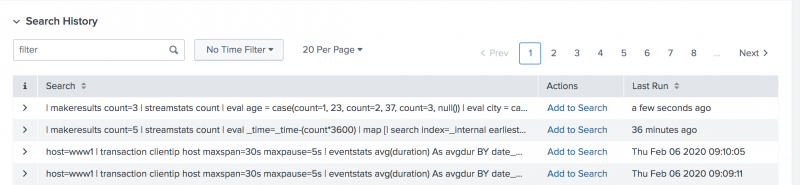
Click the greater than ( > ) symbol to expand the display to view your search history. The search history displays as a table with the following columns:
- Search
- Contains the search string, displayed as plain text so that you can copy the contents. By default, the Search History table truncates the search string to fit on a single line. For longer search strings, you can click the expand icon to the left of the search string to display the full search string.
- Actions
- Contains the action, Add to search. Click Add to Search to replace the contents of the search bar with the selected historical search contents.
- You can use keyboard shortcuts to display the search in a new browser tab.
- Windows: Use CTRL+ click on Add to Search
- Mac: Use Command + click on Add to Search
- Last Run
- Contains the date and time when the search was last run.
Filter to locate searches
You can filter your search history to quickly find the search that you are looking for. You can filter by keyword or filter by time.
- Type keywords into the filter text box to locate historical searches that contain the keyword. For example, type sourcetype=access_* to locate the searches that contain this criteria.
- Select from the list of time filters based on when the search was last run. Select either Today, Last 7 Days, or Last 30 Days. To see the entire search history, select No Time Filter.
Sort search history
In the Search History table, click the Search column header to sort the searches alphabetically by search criteria. Click the Last Run column heading to sort the searches by the date that the search was run. You can sort the list in ascending or descending order by clicking the column heading again.
Change the page display
By default, the search history shows your most recent 20 searches. Subsequent pages show older searches. Click 20 Per Page to change how many searches appear on each page in the search history list. Choose from 10, 20, or 50 searches to display on each page.
Search history with the Search Assistant
Additionally, as you type search criteria into the Search bar, the Search Assistant shows searches from your history as a possible Matching Search to the criteria you are typing in.
You can also use these keyboard shortcuts to scroll through the last 100 searches in your search history.
| Action | Linux or Windows | Mac OSX |
|---|---|---|
| Scroll to the previous search. | Alt + P | Ctrl + P |
| Scroll to the next search. | Alt + N | Ctrl + N |
See Also
| Search modes | Search command primer |
This documentation applies to the following versions of Splunk Cloud Platform™: 9.1.2312, 8.2.2112, 8.2.2201, 8.2.2202, 8.2.2203, 9.0.2205, 9.0.2208, 9.0.2209, 9.0.2303, 9.0.2305, 9.1.2308
 Download manual
Download manual
Feedback submitted, thanks!