Review current user activity
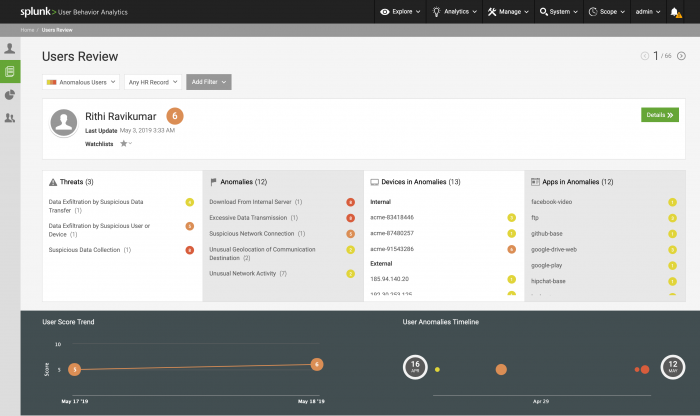
Start Users Review from the homepage of Splunk UBA to review the activity of users in your environment. Users Review shows you each user one at a time so you can focus on the riskiest users in your organization. The highest-risk users with the most recent risk-incurring activity display first. Filter the users to review by risk score, time, or add a filter to narrow the selection down by another metric, such as country.
- Review the username and last updated date and time.
- See which threats, if any, are associated with the user. Each threat has a risk score. Click a threat to see the User Threats dashboard for the selected user.
- Review the anomalies associated with the user account. Each anomaly has a risk score. Click an anomaly to see the User Anomalies dashboard for the selected user.
- Review the devices in the anomalies. Both internal and external devices could be present. Each device has a risk score. Click a device IP address to see the Device Facts dashboard.
- Review the domains in the anomalies. Click a domain to see the Domain Facts dashboard.
- Determine whether the user activity is becoming riskier over time with the User Score Trend.
- Identify clusters of anomalous behavior over time on the User Anomalies Timeline.
- If you decide to investigate the user more, or to learn more about them, click Details to see the User Facts dashboard for the user.
Add the user to a watchlist
After you review the user details, you might want to add the user to a watchlist to monitor their activities.
- Click Watchlists and select from available watchlists or create a New User Watchlist to which to add the user.
- Click Manage User Watchlists to rename or remove existing user watchlists, or add a new one.
| View user information | Delete anomalies in Splunk UBA |
This documentation applies to the following versions of Splunk® User Behavior Analytics: 5.0.0, 5.0.1, 5.0.2, 5.0.3, 5.0.4, 5.0.4.1, 5.0.5, 5.0.5.1
 Download manual
Download manual
Feedback submitted, thanks!