Anomalous System Uptime
This report provides a list of servers that have not had been rebooted in 30 days or more. Use this report to identify systems that might be vulnerable to attack.
Systems often need to be rebooted after patches are applied. Systems that have not been rebooted might still be vulnerable to compromise. PCI DSS requires that high and/or critical patches be applied within 30 days.
Relevant data sources
Relevant data sources for this report include uptime data extracted through scripts from Windows, Unix, or other hosts.
How to configure this report
1. Index uptime information captured through scripts from relevant hosts (for example, linux_base, Splunk_TA_windows).
2. Map the uptime data to the following Common Information Model fields:
dest, SystemUpTime
3. Tag the uptime data with uptime.
4. Set the should_timesync column to true for assets in the asset table that should timesync.
Report description
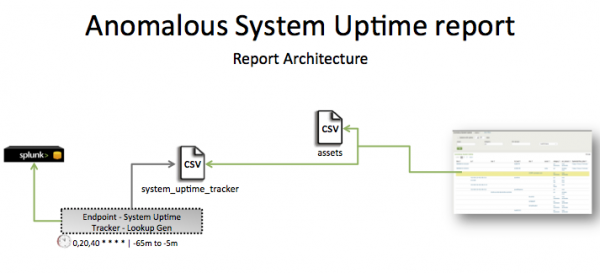
The Anomalous System Update report is populated by Endpoint - System Uptime Tracker - Lookup Gen, a lookup that runs against the system_uptime_tracker CSV file and access the assets list for additional information. This report looks at anomalous system data and uptime data extracted through scripts from Windows, Unix, or other hosts.
This search runs on an offset 20-minute cycle and looks at 60 minutes of data.
| Schedule | 0,20,40 * * * * | Runs on an offset 20 minute window. |
| Report window | -65m@m to -5m@m | Looks at 60 minutes of data. |
Note: The report window stops at 5 minutes ago because some data sources might not have provided complete data in a more recent time frame.
Useful searches and Troubleshooting
| Troubleshooting Task | Search/Action | Expected Result |
|---|---|---|
| Verify that uptime data is available in Splunk Enterprise. | tag=uptime | Returns uptime data. |
| Verify that fields are normalized and available as expected. | tag=uptime | fields dest, SystemUpTime or `uptime` |
Returns uptime data fields. |
| Verify that the uptime tracker is populated correctly. | | inputlookup append=T system_uptime_tracker or | `system_uptime_tracker` |
Returns data in system_uptime_tracker. |
| System Patch Status | PCI Command History |
This documentation applies to the following versions of Splunk® App for PCI Compliance: 2.1.1
 Download manual
Download manual
Feedback submitted, thanks!