Firewall Rule Activity
This report provides a six month rolling view of firewall rule usage to help identify unneeded, outdated, or incorrect rules. This report ensures that all rules allow only authorized services and ports that match business justifications. Compliance managers might run this report more frequently to avoid unnecessary risks and avoid opening potential security holes.
Relevant data sources
Relevant data resources include firewalls that produce rule ID information (for example, Palo Alto, Checkpoint FW).
How to configure this report
1. Index the firewall activity data that includes a rule ID in Splunk Enterprise.
2. Map the data to the following Common Information Model fields:
action, dvc, rule, transport, src, dest
3. Tag the data with “network” and “communicate”.
Note: Make sure the rule ID in the data is mapped to “rule”.
Report description
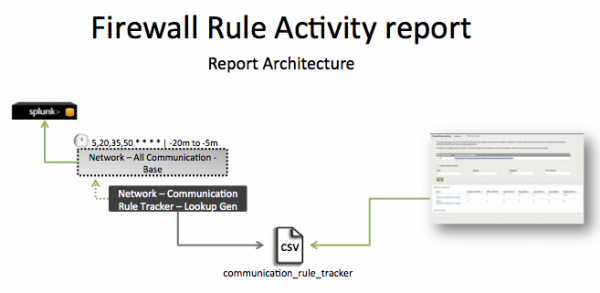
The data in the Firewall Rule Activity report is populated by Network - Communication Rule Tracker - Lookup Gen, a lookup that runs against the communication_rule_tracker CSV file. This file is created by the Network - Communication Rule Tracker - Lookup Gen lookup, which is a post-process task of the Network - All Communication - Base saved search.
This search runs on a 15-minute cycle and looks at 20 minutes of data.
| Schedule | 5,20,35,50 * * * * | Runs on a 15 offset minute window. |
| Report window | -20m@m to -5m@m | Looks at 15 minutes of data. |
Note: The report window stops at "5 minutes ago" because some data sources may not have provided complete data in a more recent time frame.
Useful searches/Troubleshooting
| Verify that... | Search/Action | Expected Result |
|---|---|---|
| Firewall data has been indexed in Splunk Enterprise. | tag=firewall tag=communicate or `communicate` |
Returns data from your network device(s). |
| The data fields are normalized to the CIM. | `communicate` | table _time,host,sourcetype,action,dvc, rule,transport,src,src_port,dest,dest_port,vendor_product |
Each field contains the correct, expected data. |
| The communication rule tracker is populated. | | inputlookup append=t communication_rule_tracker or | `communication_rule_tracker` |
Returns data in communication_rule_tracker. |
Additional Information
- The communication rule tracker file is located at
$SPLUNK_HOME/etc/apps/SA-NetworkProtection/lookups. - The “
Network – Communication – Lookup Gen” is a post-process task. You cannot find it in the Splunk Manager interface. You can find the details of this search in the$SPLUNK_HOME/etc/apps/SA-NetworkProtection/default/postprocess.conffile.
| Reports in the Splunk App for PCI Compliance | Network Traffic Activity |
This documentation applies to the following versions of Splunk® App for PCI Compliance: 2.1.1
 Download manual
Download manual
Feedback submitted, thanks!