Identity correlation
Identity correlation uses an identity list to provide information used to correlate identities (individuals) with events and assets.
What does identity correlation do?
Identity correlation provides additional information about the users involved in events. This information can be used to correlate multiple events to a single person, identify the owner of a host, determine whether an individual is subject to special attention, and more. Specifically, identity correlation provides the following:
Prioritization
The same type of access events initiated by two different users may not deserve the same level of attention; a medium severity pattern of behavior from a graphic designer's account is less urgent than the same pattern from a database administrator's account. Identity correlation allows an urgency to be computed based on the priority of individuals so that higher urgency is assigned to high priority individuals.
Categorization
Identity correlation allows information about the individuals involved to be added to events. For example, identity correlation lookups can be used in a correlation search to indicate whether the user is subject to a compliance regulation.
Normalization
Identity correlation allows accounts to be normalized and determine whether two events relate to the same individual. For example, one person may have different account names for email, ERP, and ITIL systems that they use frequently. Identify correlation helps the security analyst determine that access events for all three systems are from the same person.
Why is identity correlation important?
Identity correlation provides additional fields as part of an event to automatically designate the identity associated with the event. This makes it possible find events for an identity, and find identities for an event. Where possible, identity correlation uses session information to help match events to a session, and a session to an identity.
What is an identity?
An identity represents a user of the system. An identity can have multiple identity-related fields in the field context menu. Identity correlation will consider each of these fields in order to match the identity with the respective events.
Additionally, identities include information that describes the priority and business unit of the identity. Identities can also be put into categories to define the role of the identity or the functional area to which it belongs.
How can identity correlation be used?
The Identity Search option allows one to search for identities from anywhere that identity-related information is found in a field context menu. These searches use the Asset and Identity Search tool to look for any match in these fields. This makes it possible to:
- Update the identity lookup in the lookup editor with identities
- Automatically apply identities instantly, even for events in the past
Identity related fields are:
identity
src_user
user
user_identity
user_name
host_owner
orig_host_owner
dvc_owner
src_owner
dest_owner
How identity correlation works
Identity correlation is used to reconcile and validate the ownership of different user names that reside on systems and applications throughout the organization, and to permanently link ownership of those user names to particular individuals.
Identities (people) can operate under many different user names. For example, a person could log in as:
- jhsmith
- james_smith
- js842@gmail.com
- team.leader12
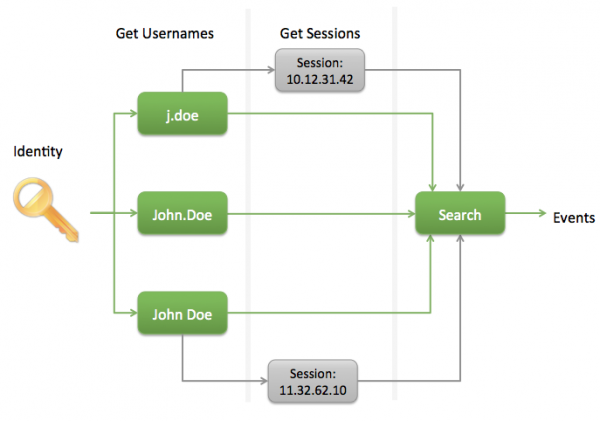
An identity search includes all of the user names for a given identity. To find events associated with an identity, Splunk searches for user names and then searches for session information to create a list of events.
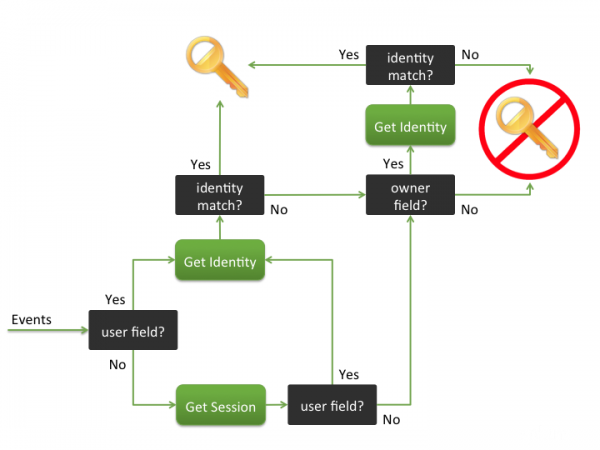
To associate an event with an identity, the event is searched for a user field, a session, or an identity field. When an identity is found, identity matching may take place to see if there are other associated user names.
Identity matching
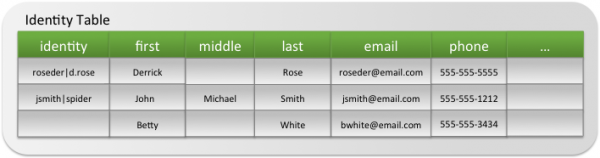
Identity matching is done by comparing user names associated with an event with identities in the Identities table. Splunk identity match configurations are specified using the identities.conf file. An Identity table might look like this:
Customizing identities
To view a current Identity list, create a new Identity list,or make immediate modifications to an existing list, go to Configure > Identities > Edit. Edit the content, or paste the new values in.
Warning: The editor does not validate input.
Alternatively, the new file may be installed at: $SPLUNK_HOME/etc/apps/SA-IdentityManagement/lookups/identities.csv.
Note: The CSV file must use UNIX line endings. The popular dos2unix utility may be used to correct line endings in a file produced on Windows or OS/X.
Update the list periodically in order to ensure that the Splunk App for Enterprise Security has reasonably up-to-date information. Generally, it is recommended that the list be updated at least every quarter.
It is possible to configure a scripted input to automatically populate the list if it is contained within a database. Automatic identity updates can be done using a combination of scripted inputs and custom search commands (written in Python). The implementation details depend on the technology that contains the identity information and is beyond the scope of this document.
Splunk automatically loads the Identity list at search time and does not need to be restarted.
The table describes the fields in the Identities list:
| Column | Description |
|---|---|
| Identity (key) | Pipe delimited list of usernames representing the identity |
| prefix | Prefix of the identity (for example, Dr.) |
| nick | Nickname of the identity |
| first | First name of the identity |
| last | Last name of the identity |
| suffix | Suffix of the identity (for example, Jr.) |
| Email address of the identity | |
| phone | Telephone number of the identity |
| phone2 | Secondary telephone number of the identity |
| managedBy | Username representing manager of the identity. |
| priority | Priority of the identity (for example, CEO = critical) |
| bunit | Business unit of the identity |
| category | Category of the identity |
| watchlist | Identity on watchlist? |
| startDate | Start/Hire date of the identity (for example, 7/3/95 15:30) |
| endDate | End/Termination date of the identity (for example, 12/31/14 19:55) |
In the Identity Center dashboard, the identities and events are aggregated by priority, by business unit, and by category. A list of identities associated with events is displayed in a table at the bottom of the dashboard. See Identity Center dashboard for more details.
| Asset management | Notable events |
This documentation applies to the following versions of Splunk® Enterprise Security: 3.0, 3.0.1
 Download manual
Download manual
Feedback submitted, thanks!