Configure the search head
The Splunk App for PCI Compliance uses summary searches to store statistical snapshots of critical data. The storage of this data depends on some architectural considerations.
The Splunk App for PCI Compliance supports the following deployment architectures:
- A Single server deployment with all data stored on the same system
- Distributed deployment with summary indexes on the search head and collected data sent to the indexer pool
- Distributed deployment with summary indexes and search head event data on the indexers
The configuration steps vary depending on which architecture you selected to use in your environment.
Single-server deployment
No additional configuration is needed. In this deployment scenario, the PCI app is installed on a single server that acts as both a search head and an indexer.
Distributed deployment with summary indexes on search head
No additional configuration is needed. This deployment architecture is common in small to medium sized deployments where the summary index volumes are low. The summary index data is generated on the search head, and is stored on the search head. Any searching that references summary indexes retrieves local results.
Distributed deployment with summary indexes on indexers
This deployment architecture is used in larger environments where the data volumes are higher and the summary indexes are expected to be larger. You must configure the search head to send all data generated locally to the indexers. Configuring the search head to forward summary data and internal events to the indexers is a "Splunk Best Practice." This configuration is also required to implement search head pooling.
To configure the search head to send all data to the indexers, configure the outputs.conf file on the search head according to "Configure forwarders with outputs.conf" in Forwarding Data.
Search head pooling considerations
The Splunk App for PCI Compliance supports search head pooling, but you should test the architecture before implementation. Search head pooling adds the potential for conflicts with other Splunk apps and has significant performance considerations. See "Key implementation issues" in Distributed Search if you plan to use a search head pool.
Update searches to use search head pooling with the Splunk App for PCI Compliance
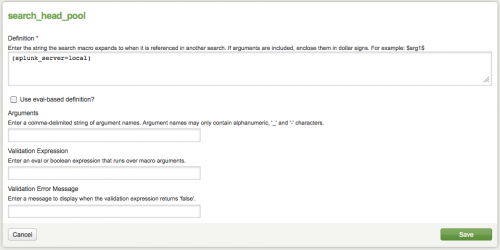
1. Navigate to the Splunk Search Head Pool configuration editor Configure > App Settings > Other Configuration Settings.
2. Click Search Head Pool.
The Search Head Pool configuration defines a list of Splunk search heads used for auditing search activity.
For search auditing, Splunk software should only evaluate search activity on servers in the Search Head pool. For example, (splunk_server=x OR splunk_server=y OR splunk_server=z).
3. Add your search heads to the pool by adding them to the list.
(splunk_server=local OR splunk_server=your_pci_server)
4. Click Save.
Use the deployment apps
The Splunk App for PCI Compliance includes a set of "deployment apps" that you can use to collect data from PCI systems and to do other useful tasks. Find out more about deployment-apps in "Using the deployment server" in this manual and "About the deployment server" in the Distributed Deployment Manual for information about the deployment server.
The deployment-apps are available in the PCI Install App. You need server access to unzip the package to get to the deployment-apps. Unzip this file:
SplunkPCIComplianceSuiteInstaller/default/src/splunk_app_pci-*.zip.
After unzipping this file, the deployment-apps are in:
SplunkPCIComplianceSuiteInstaller/default/src/etc/deployment-apps.
| Using a dedicated index for PCI data | Reports in the Splunk App for PCI Compliance |
This documentation applies to the following versions of Splunk® App for PCI Compliance: 2.1.1
 Download manual
Download manual
Feedback submitted, thanks!