PCI Resource Access
This report collects data on access attempts to PCI resources in the cardholder data environment and provides the compliance manager with visibility into all authentication attempts. Use this report to identify access attempts by users to ensure that access to cardholder data is legitimate.
You should limit access to resources in the PCI cardholder data environment to only those whose jobs require such access. This limits the risk that an account with access to cardholder data is compromised. PCI DSS requires that all authentication attempts to systems, applications, and devices in the cardholder data environment be monitored for appropriate and legitimate access.
Relevant data sources
Relevant data sources for this report include Authentication data from any system, application, or device in the cardholder data environment.
How to configure this report
1. Index all authentication attempts to applications, systems, or devices into Splunk Enterprise.
2. Map the data to the following Common Information Model fields:
host,action,app,src,src_user,dest,user
3. Tag the authentication data with authentication.
4. Add the pci category to all PCI assets in the asset table.
Report description
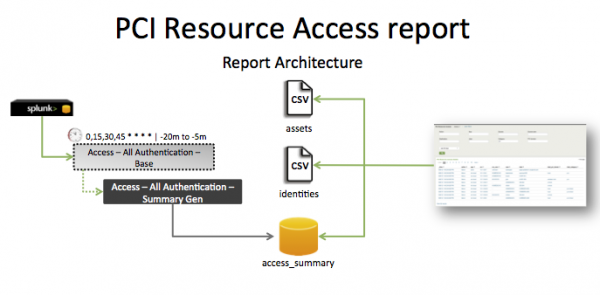
The data in the PCI Resource Access report is populated by a lookup that runs against the Access_summary index. The Access - All Authentication - Summary Gen lookup, which is a post-process task of the Access - All Authentication - Base saved search, creates this index.
This search runs on a 15-minute cycle and looks at 15 minutes of data.
| Schedule | 0,15,30,45 * * * * | Runs on an offset 15-minute window. |
| Report window | -20m@m to -5m@m | Looks at 15 minutes of data. |
Note: The report window stops at 5 minutes ago, because some data sources may not have provided complete data in a more recent time frame.
Useful searches/Troubleshooting
| Troubleshooting Task | Search/Action | Expected Result |
|---|---|---|
| Verify that you have data from your system, application, or device. | sourcetype=<expected_st> | Returns data from your network device, or devices. |
| Verify that the authentication data is tagged correctly. | tag=authentication or `authentication` |
Returns authentication data. |
| Verifty that fields are normalized and available as expected. | `authentication` | table _time, host, action, app, src, src_user, dest, user | Returns a table of authentication data fields. |
| Verify that the access summary is populated correctly. | `get_summary(access_summary,Access - All Authentication - Summary Gen)` | Returns data in access_summary index. |
Additional information
- The report displays all attempts from users in either the
src_useroruserfields. - The identities table includes service accounts that appear as users, such as
root, andnetwork service. Depending upon the compliance policy, these accounts can be removed from the resulting reports by two methods: - Remove the accounts entirely from the identities table in Configure > Lists and Lookups > Identities.
- Modify the saved search that generates the report to exclude those accounts.
| PCI Command History | Endpoint Changes |
This documentation applies to the following versions of Splunk® App for PCI Compliance: 2.1.1
 Download manual
Download manual
Feedback submitted, thanks!