Endpoint Product Deployment
This report provides a summary and detail view of all PCI assets and the most current product versions installed. Use this report to identify any assets that are not using the current antimalware product versions and take appropriate measures to ensure these systems are updated. Review this report at least once per day. Review this report more frequently if you are collecting data from antimalware solutions more frequently.
PCI DSS requires that assets within the cardholder data environment have antimalware technology installed and working to protect against viruses, worms, trojans, and other malware-based threats. The best antimalware software has limited effectiveness if it does not have the current antivirus product versions.
Relevant data sources
Relevant data sources for this report include antivirus activity, endpoint version data, or endpoint product signature data. This report looks at endpoint protection deployment activity data produced by firewalls, routers, switches, and any other device that produces endpoint data.
How to configure this report
1. Index endpoint product version data, signature data, and/or activity data from an antivirus or other endpoint protection software.
2. Map the data to the following Common Information Model fields:
dest, product_version, vendor_product
3. Tag the activity data with endpoint, application, and version.
Report description
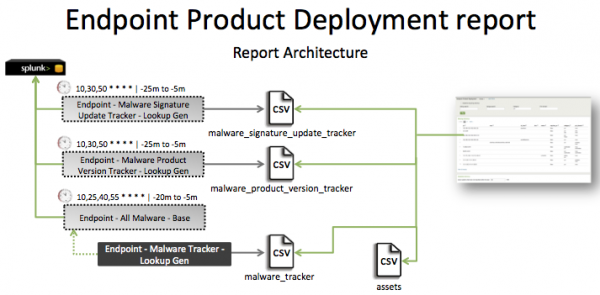
The data in the Endpoint Product Deployment report is populated by a lookup that runs against the malware_product_version_tracker CSV file. This file is created by the Endpoint - Malware Product Version Tracker - Lookup Gen lookup.
This report includes three searches: Endpoint - Malware Product Update Tracker - Lookup Gen, Endpoint - Malware Product Version Tracker - Lookup Gen, and Endpoint - All Malware - Base.
The Endpoint - Malware Product Update Tracker - Lookup Gen search runs on an offset 20 minute cycle and looks at 15 minutes of data.
| Schedule | 10,30,50 * * * * | Runs on an offset 20 minute window. |
| Report window | -25m@m to -5m@m | Looks at 20 minutes of data. |
The Endpoint - Malware Product Version Tracker - Lookup Gen search runs on an offset 20 minute cycle and looks at 15 minutes of data.
| Schedule | 10,30,50 * * * * | Runs on an offset 20 minute window. |
| Report window | -25m@m to -5m@m | Looks at 20 minutes of data. |
The Endpoint - All Malware - Base search runs an offset 15 minute cycle and looks at 15 minutes of data.
| Schedule | 10,25,40,55 * * * * | Runs on an offset 15 minute window. |
| Report window | -20m@m to -5m@m | Looks at 15 minutes of data. |
Refer to the Report Architecture graphic for details.
Note: The report window stops at 5 minutes ago because some data sources may not have provided complete data in a more recent time frame.
Useful searches/Troubleshooting
| Troubleshooting Task | Search/Action | Expected Result |
|---|---|---|
| Verify that endpoint product signature data is present. | tag=endpoint tag=application tag=signature tag=update | Returns endpoint product signature data. |
| Verify that endpoint product version data is present. | tag=endpoint tag=application tag=version | Returns endpoint protection deployment data. |
| Verify that malware activity data is present. | tag=malware tag=attack | Returns malware activity data. |
| Verify that endpoint product signature data fields are normalized. | tag=endpoint tag=application tag=signature tag=update | table signature_version,dest,vendor_product | Returns a table of endpoint product signature data. |
| Verify that endpoint product version data fields are normalized. | tag=endpoint tag=application tag=version | table dest,product_version,vendor_product | Returns table of endpoint protection deployment fields. |
| Verify that malware activity data fields are normalized. | `malware` | table _time, host, action, category, signature, dest, dest_nt_domain, user, vendor_product | Returns a table of malware activity data fields. |
| Verify that the endpoint product version tracker file has been populated as expected. | | inputlookup append=T malware_product_version_tracker or |`malware_product_version_tracker` |
Returns data in the endpoint product version tracker. |
| Verify that the endpoint product signature tracker file has been populated as expected. | | inputlookup append=T malware_signature_update_tracker or | `malware_signature_update_tracker` |
Returns data in the endpoint product signature tracker. |
| Verify that the malware activity summary index has been populated as expected. | `get_summary(endpoint_summary,Endpoint - All Malware - Summary Gen)` | Returns data in the malware activity summary index. |
| Verify that the data from the three trackers and the asset table have been joined and is producing the correct result. | | `malware_product_deployment_tracker` | Returns data in the malware_product_version_tracker. |
Additional information
- The
Access – All Authentication – Summary Genis a post-process task. You can find the details of this search in the$SPLUNK_HOME/etc/apps/SA-AccessProtection/default/postprocess.conffile.
The following lookups are also used:
- Search:
Endpoint - All Malware - Base--> post process:Endpoint - Malware Tracker - Lookup Gen, which populates the lookupmalware_tracker - Search:
Endpoint - Malware Signature Update Tracker - Lookup Gen, which populates the lookupmalware_signature_update_tracker
| Credit Card Data Found | Endpoint Product Versions |
This documentation applies to the following versions of Splunk® App for PCI Compliance: 2.1.1
 Download manual
Download manual
Feedback submitted, thanks!