System Misconfigurations
This report provides a view of all identified system misconfigurations on PCI-relevant assets in your cardholder environment. Use this report to compare the identified misconfigurations with the defined hardening policy to determine the level of risk to the asset.
Malicious individuals often use vendor default configuration settings to compromise systems and applications. These settings are well known in hacker communities and leave systems highly vulnerable to attack. This report ensures your organization's system configuration standards and related processes specifically address security settings and parameters that have known security implications.
Relevant data sources
Relevant data for this report includes data from configuration assessment tools that identify a misconfigured setting on an endpoint (for example, Qualys, IBM/Tivoli, SCAP scanner tools).
How to configure this report
1. Index misconfiguration data in Splunk Enterprise.
2. Map the data to the following Common Information Model fields:
host, ids_type, category, signature, severity, src, dest, vendor_product
3. Tag misconfiguration events with misconfiguration.
Report description
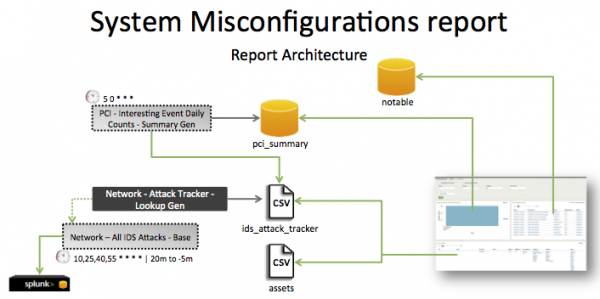
The data in the System Misconfiguration report is populated by an ad hoc search that runs against the pci_summary summary index. This index is created by the PCI - Interesting Event Daily Counts - Summary Gen saved search, which is a post-process task of the Network - All IDS Attacks - Base saved search.
The Network - All IDS Attacks - Base search runs on a 15 minute cycle and looks at 15 minutes of data.
| Schedule | 10,25,40,55 * * * * | Runs on a 15 minute offset window. |
| Report window | -20m@m to -5m@m | Looks at 15 minutes of data. |
Note: The report window stops at 5 minutes ago because some data sources may not have provided complete data in a more recent time frame.
Useful searches/Troubleshooting
| Troubleshooting Task | Search/Action | Expected Result |
|---|---|---|
| Verify that data is present. | `ids_attack` | search tag=misconfiguration | Returns system misconfiguration data. |
| Verify that fields are normalized and available. | `ids_attack` | search tag=misconfiguration | tags outputfield=tag | table _time,host, sourcetype,dvc,ids_type,category,signature,severity,src,dest,tag,vendor_product |
Returns a table of system misconfiguration fields. |
| Verify that the summary index is populated by the post-process saved search. | `get_summary(pci_summary, PCI - Interesting Event Daily Counts - Summary Gen)` | search tag=misconfiguration | Returns data in the pci_summary index. |
Additional information
This report uses default source types that ship with windows TA + linux_base deployment package.
The Access – All Authentication – Summary Gen is a post-process task. You can find the details of this search in the $SPLUNK_HOME/etc/apps/SA-AccessProtection/default/postprocess.conf file.
| Prohibited Services | Wireless Network Misconfigurations |
This documentation applies to the following versions of Splunk® App for PCI Compliance: 2.1.1
 Download manual
Download manual
Feedback submitted, thanks!