IDS/IPS Alert Activity
Intrusion detection and/or prevention systems (IDS/IPS) compare inbound and outbound network traffic against known signatures and/or behaviors of thousands of compromise types (hacker tools, Trojans and other malware). This report collects data on unauthorized wireless access points found on the network and provides a summarized view of the intrusion activity involving an asset in the PCI domain. Use this report to identify attack trends and behavior that could indicate a more significant threat.
Intrusion detection and/or prevention systems can be configured to either alert or stop the intrusion attempt. Without a proactive approach to unauthorized activity detection using these tools, attacks on (or misuse of) PCI resources could go unnoticed in real time. PCI requires that the alerts generated by these tools be monitored so that attempted intrusions can be stopped before they happen.
Relevant data sources
Relevant data sources for this report include IDS/IPS systems, network scan results, or Network Access Control (NAC) logs.
How to configure this report
1. Index IDS/IPS alert data in Splunk Enterprise.
2. Map the IDS/IPS data to the following Common Information Model fields:
dvc, ids_type, category, signature, severity, src, dest
3. Tag the successful synchronization data with ids and attack.
Report description
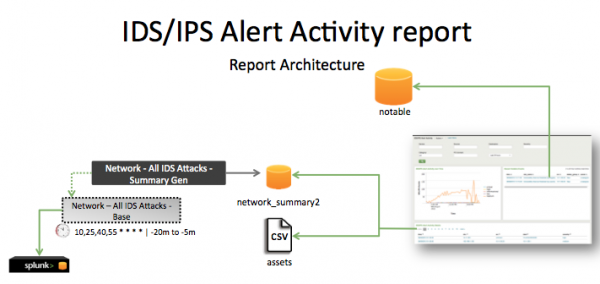
The data in the IDS/IPS report is populated by an ad hoc search that runs against the network_summary2 and the assets list. This lookup created by the Network - All IDS Attacks - Summary Gen saved search, which is a post-process task of the Network - All IDS Attacks - Base saved search. This information is combined with information from the assets table to produce the report.
This search runs on an offset 15-minute cycle and looks at 15 minutes of data.
| Schedule | 10,25,40,55 * * * * | Runs on an offset 15-minute schedule. |
| Report window | -20m@m to -5m@m | Looks at 15 minutes of data. |
Note: The report window stops at 5 minutes ago because some data sources might not have provided complete data in a more recent time frame.
Useful searches/Troubleshooting
| Troubleshooting Task | Search/Action | Expected Result |
|---|---|---|
| Verify that IDS/IPS data has been indexed in Splunk Enterprise. | tag=ids tag=attack or `ids_attack` |
Returns IDS/IPS data. |
| Verify that fields are normalized and available at search time. | `ids_attack` | tags outputfield=tag | table _time, host, sourcetype, dvc, ids_type, category, signature, severity, src, dest, tag, vendor_product | Returns a table of IDS/IPS data fields. |
| Verify that the IDS attack summary gen file is populated. | `get_summary(network_summary2,Network - All IDS Attacks - Summary Gen)` | Returns IDS attact data in the networki_summary2 index. |
| Rogue Wireless Access Point Protection | Configure correlation searches |
This documentation applies to the following versions of Splunk® App for PCI Compliance: 2.1.1
 Download manual
Download manual
Feedback submitted, thanks!