Wireless Network Misconfigurations
The report tracks misconfigurations found on wireless network devices. This report provides visibility into data collected from IDS/IPS, NAC, network scanners, and other sources of data. This report displays a list of misconfigurations found on wireless access devices. Use this report to view the misconfiguration information and continuously monitor the data to identify devices that are not configured properly.
Implementation and/or exploitation of wireless technology within a network is one of the most common paths for malicious users to gain access to the network and cardholder data. Corporate controlled or rogue access devices that are not configured with appropriate security configurations can allow an attacker to invisibly enter the network and put cardholder data at risk.
Note: This report does not display unencrypted traffic directly, only misconfigurations that indicate the possible transmission or side-channel leakage of unencrypted traffic. For a full traffic report, see "Network Traffic Activity" in the Installation and Configuration Manual.
Relevant data sources
Relevant data sources include misconfiguration data found by wireless network monitoring products or IDS systems. Relevant data sources also include data collected from IDS/IPS, NAC, network scanners, and other similar sources of data.
How to configure this report
1. Index network misconfiguration data in Splunk Enterprise.
2. Map the data to the following Common Information Model fields:
host, ids_type, category, signature, severity, src, dest, vendor_product
3. Tag wireless misconfiguration events with misconfiguration and wireless.
Report description
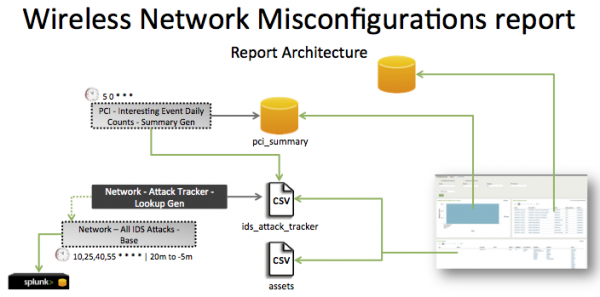
The data in the Wireless System Misconfiguration report is populated by a search that runs against the pci_summary summary index. This index is created by the PCI - Interesting Event Daily Counts - Summary Gen saved search, which is a post-process task of the Network - All IDS Attacks - Base saved search.
The Network - All IDS Attacks - Base search runs on a 15 minute offset cycle and looks at 15 minutes of data.
| Schedule | 10,25,40,55 * * * * | Runs on an offset 15 minute window. |
| Report window | -20m@m to -5m@m | Looks at 15 minutes of data. |
Note: The report window stops at 5 minutes ago because some data sources may not have provided complete data in a more recent time frame.
Useful searches/Troubleshooting
| Troubleshooting Task | Search/Action | Expected Result |
|---|---|---|
| Verify that data is present. | tag=misconfiguration tag=wireless | Returns wireless system misconfiguration data. |
| Verify that fields are normalized and available. | `ids_attack` | search tag=misconfiguration tag=wireless | tags outputfield=tag | table _time,host,sourcetype,dvc,ids_type,category,signature,severity,src,dest, tag,vendor_product |
Returns a list of events and the specific wireless system misconfiguration fields of data populated. |
| Verify that the pci_summary index is populated by the post-process saved search. | `get_summary(pci_summary, PCI - Interesting Event Daily Counts - Summary Gen)` | search tag=misconfiguration tag=wireless | Returns data in the pci_summary index. |
Additional information
- The primary functions list can be found at Configure > Lists and Lookups > Primary Functions.
- The primary functions CSV file can be found
$SPLUNK_HOME/
- The “
Access – All Authentication – Summary Gen” is a post-process task. You can find the details of this search in the$SPLUNK_HOME/etc/apps/SA-AccessProtection/default/postprocess.conffile.
| System Misconfigurations | Credit Card Data Found |
This documentation applies to the following versions of Splunk® App for PCI Compliance: 2.1.1
 Download manual
Download manual
Feedback submitted, thanks!