Malware Activity
This report looks at malware activity data on cardholder systems produced by antimalware solutions or any other device that produces malware activity data. It looks at data from IDS, IPS, and DLP systems, to provide visibility into potentially unauthorized transmissions of credit card data over the network or to unauthorized removable storage devices.
Use this report to identify the source of the transmission so it can be further investigated and fixed. The cardholder data environment should be monitored for unauthorized transmission of credit card data using IDS, IPS, and DLP based technologies. PCI requires that cardholder data be protected from unauthorized access or distribution.
Relevant data sources
Relevant data sources include alerts from IDS, IPS, or DLP solutions and from the Splunk Luhn-based log evaluation.
How to configure this report
Make sure the activity data you are monitoring conforms to the malware sections of the Common Information Model.
1. Index malware activity data from antivirus software in Splunk Enterprise.
2. Map the data to the following Common Information Model fields:
action, category, signature, dest, dest_nt_domain, user, file_name, file_path, file_hash
3. Tag the activity data with malware and attack.
Report description
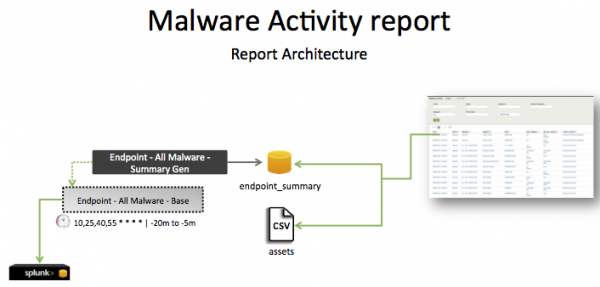
The data in the Malware Activity report is populated by an ad hoc search that runs against the endpoint_summary summary index. This index is created by the Endpoint - All Malware - Summary Gen saved search, which is a post-process task of the Endpoint - All Malware - Base saved search.
This search runs on an offset 15 minute cycle and looks at 15 minutes of data.
| Schedule | 10,25,40,55 * * * * | Runs on an offset 15 minute window. |
| Report window | -20m@m to -5m@m | Looks at 15 minutes of data. |
Note: The report window stops at 5 minutes ago because some data sources may not have provided complete data in a more recent time frame.
Useful searches/Troubleshooting
| Troubleshooting Task | Search/Action | Expected Result |
|---|---|---|
| Verify that data is present. | tag=malware tag=attack | Returns malware activity data. |
| Verify that fields are normalized and available as expected. | `malware` | table _time,host,action,category,signature,dest, dest_nt_domain,user,vendor_product |
Returns a table of events and the specific malware activity fields for malware activity data. |
| Verify that the summary index is populated by the post-process saved search. | `get_summary(endpoint_summary,Endpoint - All Malware - Summary Gen)` | Returns data in the endpoint_summary index. |
Additional information
Access – All Authentication – Summary Genis a post-process task. You can find the details of this search in the$SPLUNK_HOME/etc/apps/SA-AccessProtection/default/postprocess.conffile.
| Endpoint Product Versions | Malware Signature Updates |
This documentation applies to the following versions of Splunk® App for PCI Compliance: 2.1.1
 Download manual
Download manual
Feedback submitted, thanks!