Rogue Wireless Access Point Protection
This report gathers data on unauthorized wireless access points found on the network. It uses the data generated by IDS/IPS systems, network scan results, or Network Access Control (NAC) logs to report on any rogue access device detections. Use this report to see any discovered rogue access devices and more deeply explore the network, user activity, or system activity to further investigate the access points.
Implementation and/or exploitation of wireless technology within a network is one of the most common paths for malicious users to gain access to the network and cardholder data. If a wireless device or network is installed without a company's knowledge, it can allow an attacker to easily and invisibly enter the network. PCI compliance requires that organizations test for the presence of wireless access devices on the network at least once every three months. More frequent testing is recommended.
Relevant data sources
Relevant data sources for this report include IDS/IPS systems, network scan results, or Network Access Control (NAC) logs.
How to configure this report
1. Index wireless access detection data in Splunk Enterprise.
2. Map the wireless access detection data to the following Common Information Model fields:
dvc, ids_type, category, signature, severity, src, dest
3. Tag the successful synchronization data with rogue and wireless.
Report description
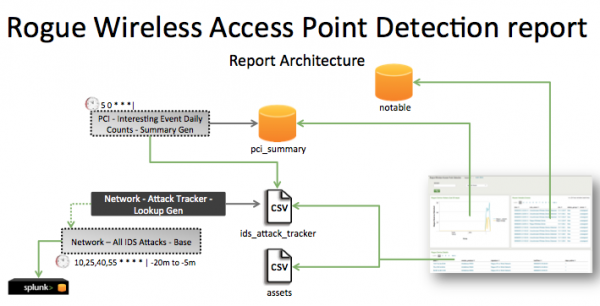
The data in the Rogue Wireless Access Point Protection report is populated by a search that runs against the ids_attack_tracker lookup. This lookup is created by the Network - Attack Tracker - Lookup Gen saved search, which is a post-process task of the Network - All IDS Attacks - Base saved search. This lookup is populated by the pci_index, which gets data from the PCI - Interesting Event Daily Counts - Summary Gen saved search.
This search runs on an offset 15-minute cycle and looks at 15 minutes of data.
| Schedule | 10,25,40,55 * * * * | Runs on an offset 15-minute schedule. |
| Report window | -20m@m to -5m@m | Looks at 15 minutes of data. |
Note: The report window stops at 5 minutes ago because some data sources might not have provided complete data in a more recent time frame.
Useful searches and Troubleshooting
| Troubleshooting Task | Search/Action | Expected Result |
|---|---|---|
| Verify that you have rogue wireless access point data. | sourcetype=<expected_st> | Returns rogue wireless access point data. |
| Verify that wireless access data from an IDS, network scan, or network scan is in Splunk Enterprise. | tag=rogue tag=wireless | Returns rogue wireless access point protection data. |
| Verify that fields are normalized and available at search time. | search tag=rogue tag=wireless tag=pci | _time,host,sourcetype,dvc,ids_type,category,signature, severity,src,dest,tag,vendor_product |
Returns rogue wireless access point protection data fields. |
| Verify that the ids attack tracker file is populated. | | inputlookup ids_attack_tracker or `ids_attack_tracker` |
Returns data in the ids attack tracker. |
| Verify that the pci_summary index is populated. | `get_summary(pci_summary, PCI - Interesting Event Daily Counts - Summary Gen)` | Returns rogue wireless access point protection data in the pci_summary index. |
| Vulnerability Scan Details | IDS/IPS Alert Activity |
This documentation applies to the following versions of Splunk® App for PCI Compliance: 2.1.1
 Download manual
Download manual
Feedback submitted, thanks!